
Continuous Human Verification for Legal Teams
Prove Exactly Who Viewed Your Confidential Data.
YEO delivers out-of-band human verification and immutable Evidence of Sight for CRB-compliant audit trails that go beyond device-level MFA. Know exactly who saw the file: not just who logged in.


Continuous Human Verification for Legal Teams
Prove Exactly Who Viewed Your Confidential Data.
YEO delivers out-of-band human verification and immutable Evidence of Sight for CRB-compliant audit trails that go beyond device-level MFA. Know exactly who saw the file: not just who logged in.


Prove Exactly Who Viewed Your Confidential Data.
YEO delivers out-of-band human verification and immutable Evidence of Sight for CRB-compliant audit trails that go beyond device-level MFA. Know exactly who saw the file: not just who logged in.

THE PROBLEM
Why Standard Encryption Fails the Human Test
Encryption protects the file in transit, but creates a "dark zone" the moment the document is opened on a recipient's device.

THE PROBLEM
Why Standard Encryption Fails the Human Test
Encryption protects the file in transit, but creates a "dark zone" the moment the document is opened on a recipient's device.

THE PROBLEM
Why Standard Encryption Fails the Human Test
Encryption protects the file in transit, but creates a "dark zone" the moment the document is opened on a recipient's device.

Regulatory Requirement
Regulators no longer accept ‘sent’ as proof. The CRB 24-hour mandate requires proof of who saw the data.
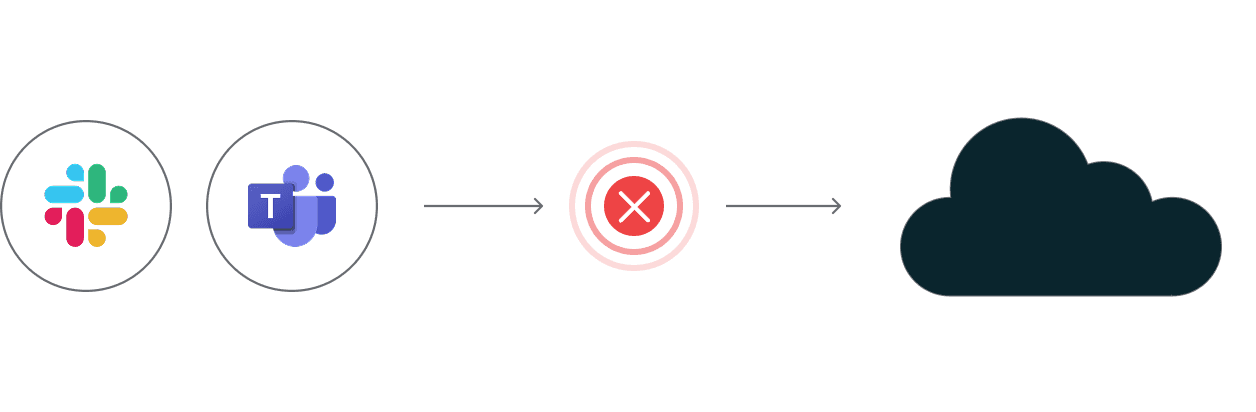
The MFA Blindspot
Standard MFA verifies the device at login, but ignores the human at the screen during the viewing session.

The In-Band Risk
If the primary network is compromised, "in-band" verification tokens are equally vulnerable to interception.
The Delivery Delusion
"Delivered" status in an email header is not legal proof of recipient integrity.

Regulatory Requirement
Regulators no longer accept ‘sent’ as proof. The CRB 24-hour mandate requires proof of who saw the data.
The MFA Blindspot
Standard MFA verifies the device at login, but ignores the human at the screen during the viewing session.

The In-Band Risk
If the primary network is compromised, "in-band" verification tokens are equally vulnerable to interception.
The Delivery Delusion
"Delivered" status in an email header is not legal proof of recipient integrity.

Regulatory Requirement
Regulators no longer accept ‘sent’ as proof. The CRB 24-hour mandate requires proof of who saw the data.
The MFA Blindspot
Standard MFA verifies the device at login, but ignores the human at the screen during the viewing session.

The In-Band Risk
If the primary network is compromised, "in-band" verification tokens are equally vulnerable to interception.
The Delivery Delusion
"Delivered" status in an email header is not legal proof of recipient integrity.

Compare YEO with Legacy Infrastructure
YEO
Encrypted Email
Standard MFA
Out-of-Band Architecture
Continuous Human Verification
Evidence of Sight Reports
Hardware-Locked Geofencing
CRB-Ready Audit Trails
Compare YEO with Legacy Infrastructure
YEO
Encrypted Email
Standard MFA
Out-of-Band Architecture
Continuous Human Verification
Evidence of Sight Reports
Hardware-Locked Geofencing
CRB-Ready Audit Trails
Compare YEO with Legacy Infrastructure
YEO
Encrypted Email
Standard MFA
Out-of-Band Architecture
Continuous Human Verification
Evidence of Sight Reports
Hardware-Locked Geofencing
CRB-Ready Audit Trails
Out-of-Band (OOB) Authentication Architecture
Establishing an independent, face-locked channel for sensitive disclosures that bypasses the primary firm network.

Sovereign Encryption
End-to-end encryption with zero key access. YEO never holds message content — preserving absolute client-counsel confidentiality.
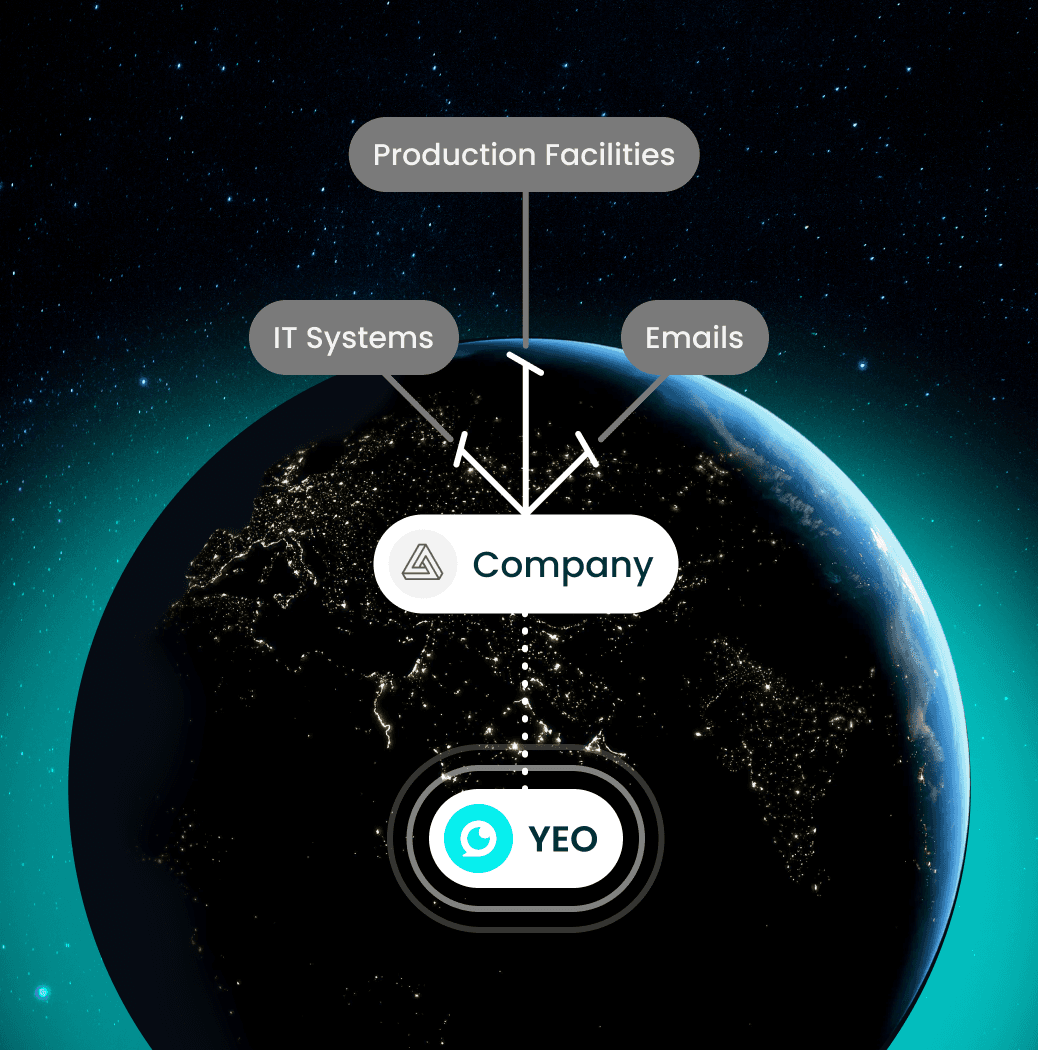
OOB Handshake
Verification runs through a secondary, independent channel — eliminating single-point network risk.

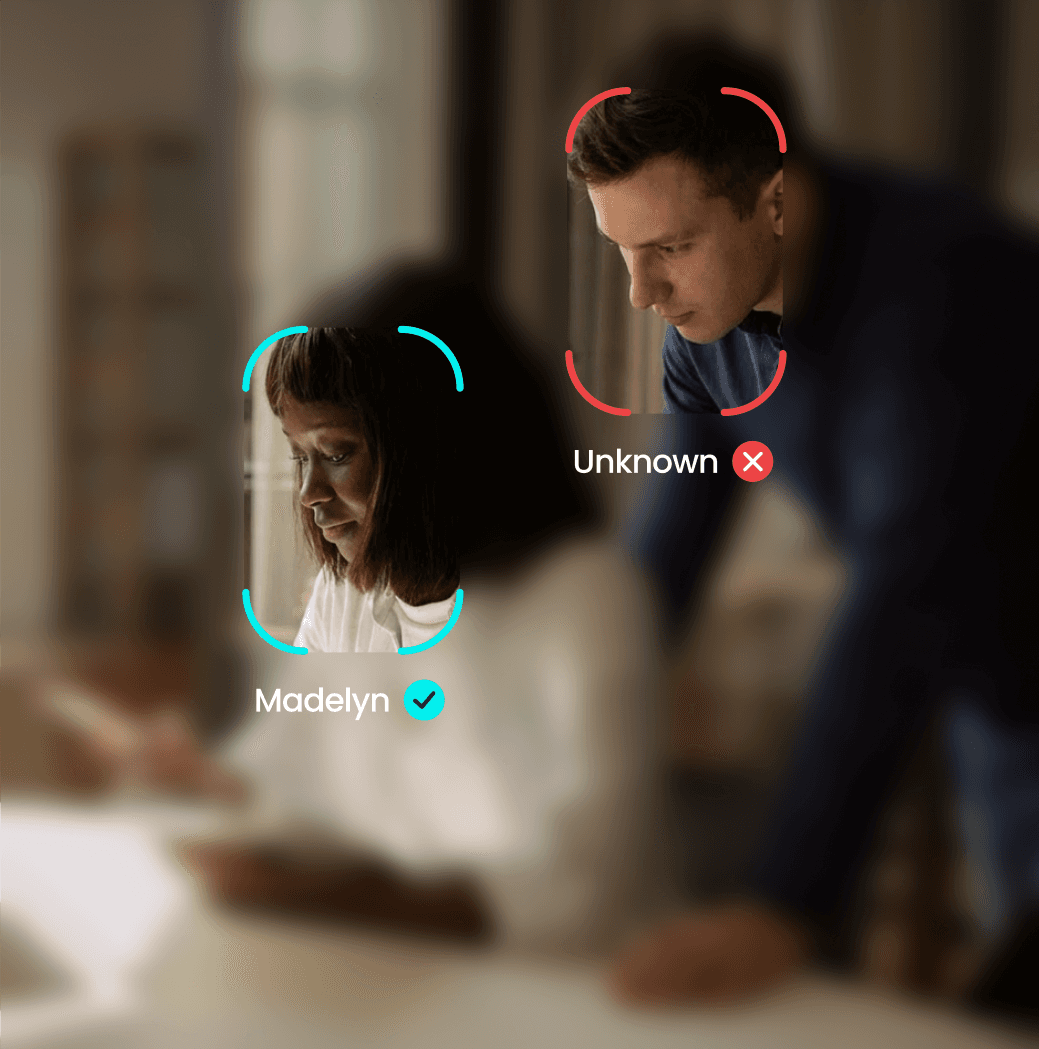
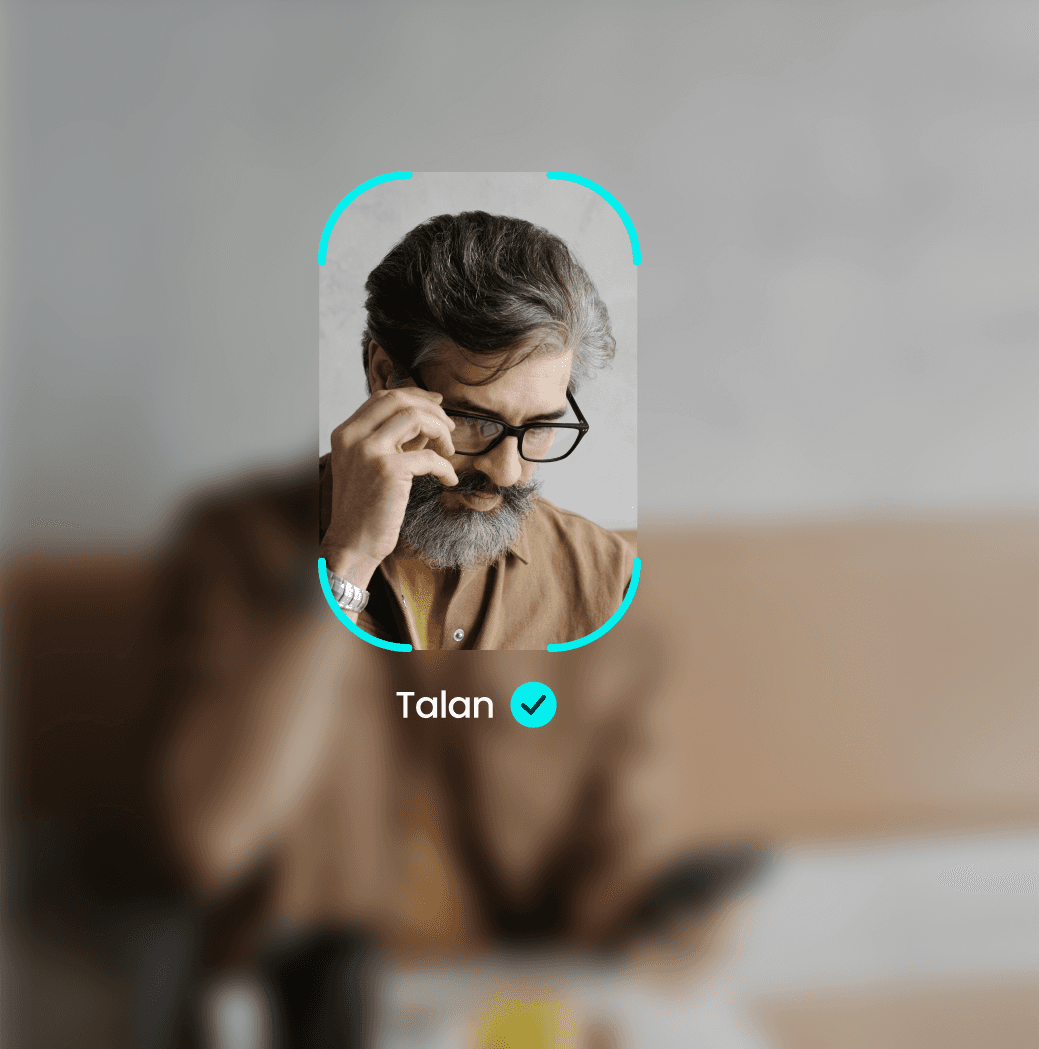
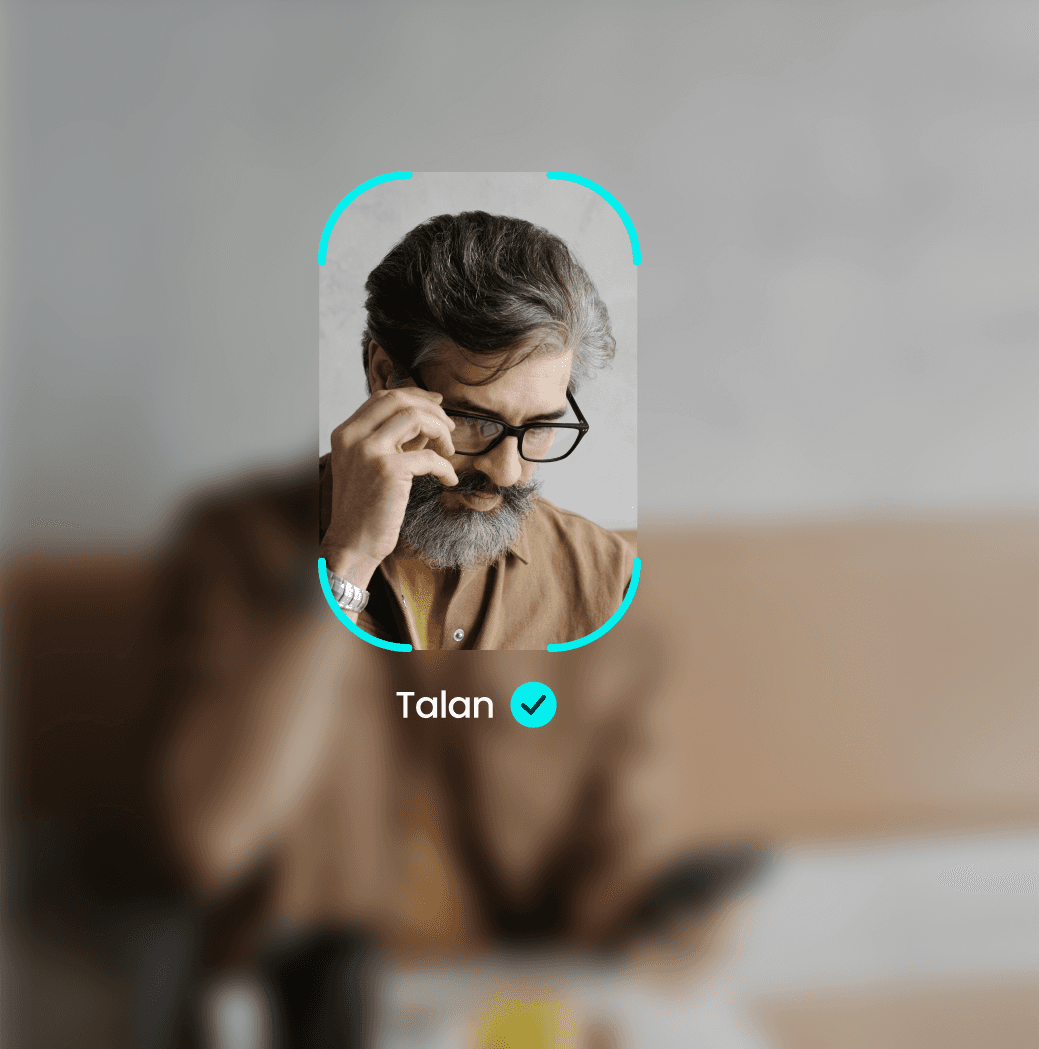
Continuous Human Verification
Face-locked liveness detection confirms the intended recipient remains present throughout the viewing session.

Chain of Custody
Metadata-rich Evidence of Sight reports generated instantly for compliance filing.
STEP 1
Send Secure Message
STEP 2
Biometric Verification
STEP 3
Recipient Opens
STEP 4
Evidence of Sight Logged
Out-of-Band (OOB) Authentication Architecture
Establishing an independent, face-locked channel for sensitive disclosures that bypasses the primary firm network.

Sovereign Encryption
End-to-end encryption with zero key access. YEO never holds message content — preserving absolute client-counsel confidentiality.
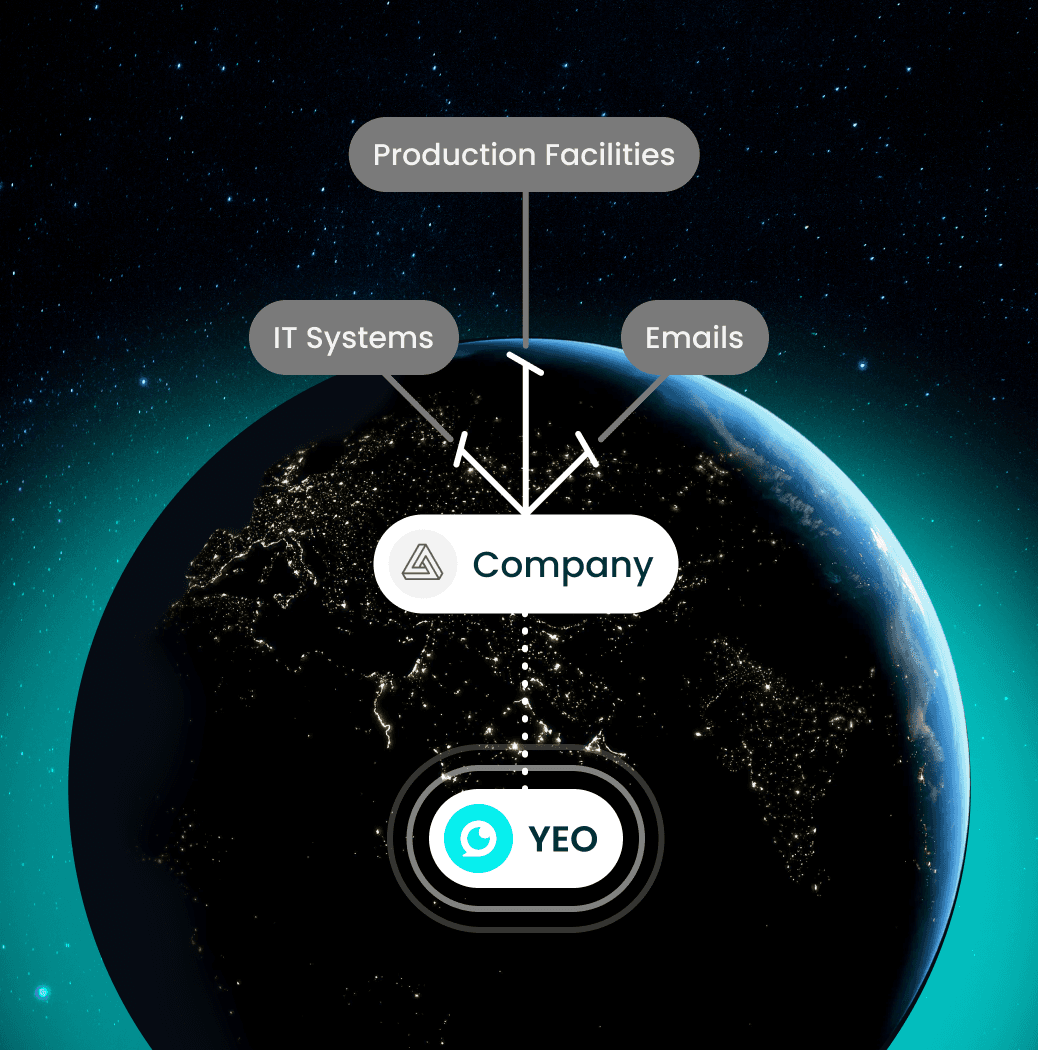
OOB Handshake
Verification runs through a secondary, independent channel — eliminating single-point network risk.

Continuous Human Verification
Face-locked liveness detection confirms the intended recipient remains present throughout the viewing session.

Chain of Custody
Metadata-rich Evidence of Sight reports generated instantly for compliance filing.
STEP 1
Send Secure Message
STEP 2
Biometric Verification
STEP 3
Recipient Opens
STEP 4
Evidence of Sight Logged
Out-of-Band (OOB) Authentication Architecture
Establishing an independent, face-locked channel for sensitive disclosures that bypasses the primary firm network.

Sovereign Encryption
End-to-end encryption with zero key access. YEO never holds message content — preserving absolute client-counsel confidentiality.
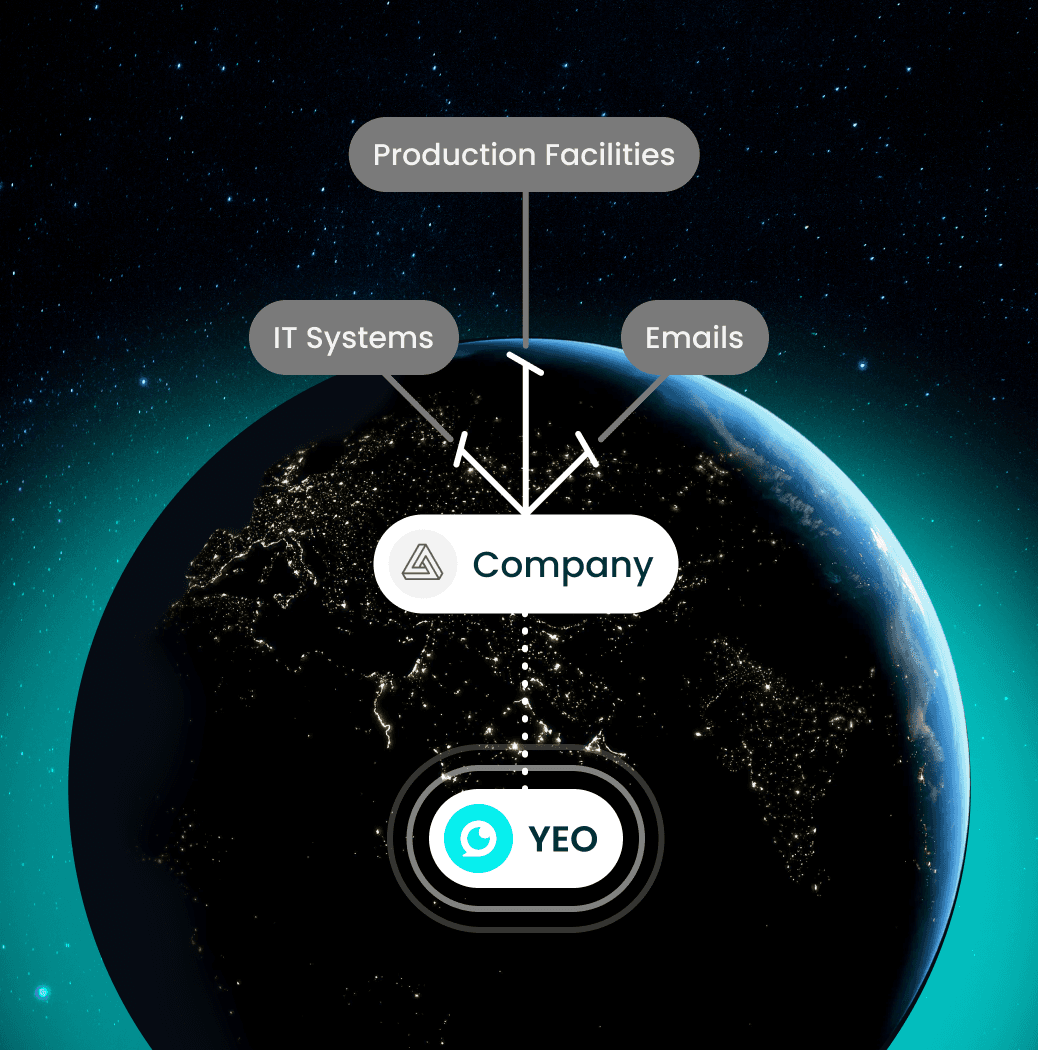
OOB Handshake
Verification runs through a secondary, independent channel — eliminating single-point network risk.

Continuous Human Verification
Face-locked liveness detection confirms the intended recipient remains present throughout the viewing session.

Chain of Custody
Metadata-rich Evidence of Sight reports generated instantly for compliance filing.
STEP 1
Send Secure Message
STEP 2
Biometric Verification
STEP 3
Recipient Opens
STEP 4
Evidence of Sight Logged
Enterprise-Grade Security. Minimal Workflow Change.
YEO isn't just about secure communication—it’s about creating a trusted, compliant, and resilient communication ecosystem for your business.
Matter-Specific Piloting
Start with a single matter or high-risk case before firm-wide rollout.
Continuous Identity Verification
Users are continuously verified during sensitive communications to prevent impersonation.
Incident-Ready Evidence
Generate cryptographic proof of communication events for rapid investigation and forensic review.
Rapid Deployment
Deployable across specific teams or departments in under 48 hours.
Client-First Privacy
No sensitive message content is ever stored on YEO servers.
Zero Disruption
No change to existing email or document management workflows.

Enterprise-Grade Security. Minimal Workflow Change.
YEO isn't just about secure communication—it’s about creating a trusted, compliant, and resilient communication ecosystem for your business.
Matter-Specific Piloting
Start with a single matter or high-risk case before firm-wide rollout.
Continuous Identity Verification
Users are continuously verified during sensitive communications to prevent impersonation.
Incident-Ready Evidence
Generate cryptographic proof of communication events for rapid investigation and forensic review.
Rapid Deployment
Deployable across specific teams or departments in under 48 hours.
Client-First Privacy
No sensitive message content is ever stored on YEO servers.
Zero Disruption
No change to existing email or document management workflows.

Enterprise-Grade Security. Minimal Workflow Change.
YEO isn't just about secure communication—it’s about creating a trusted, compliant, and resilient communication ecosystem for your business.

Continuous Facial Recognition
Blocks deepfakes and recordings
Evidence of Sight
Hard-code recipient integrity into every message
Continuous Verification
Face-locked and geofenced security
Zero-Knowledge Encryption
We can’t read your privileged data
Pre-Staged Client Groups
One-tap verified notification
Biometric Audit Trail
Undeniable proof for regulatory compliance

Hard-Coded Recipient Integrity



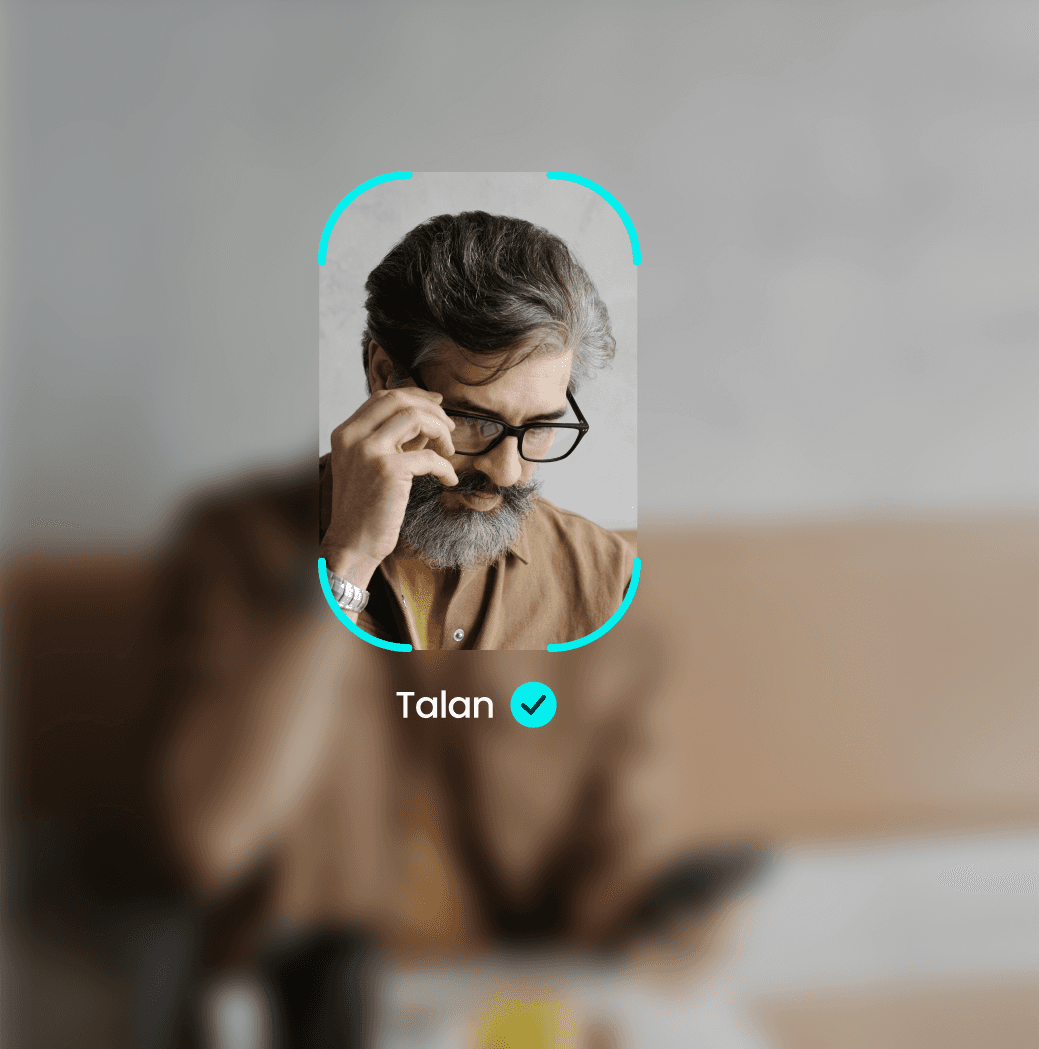
Evidence of Sight
Biometric confirmation that the intended eyes, and only those eyes, are on the screen.
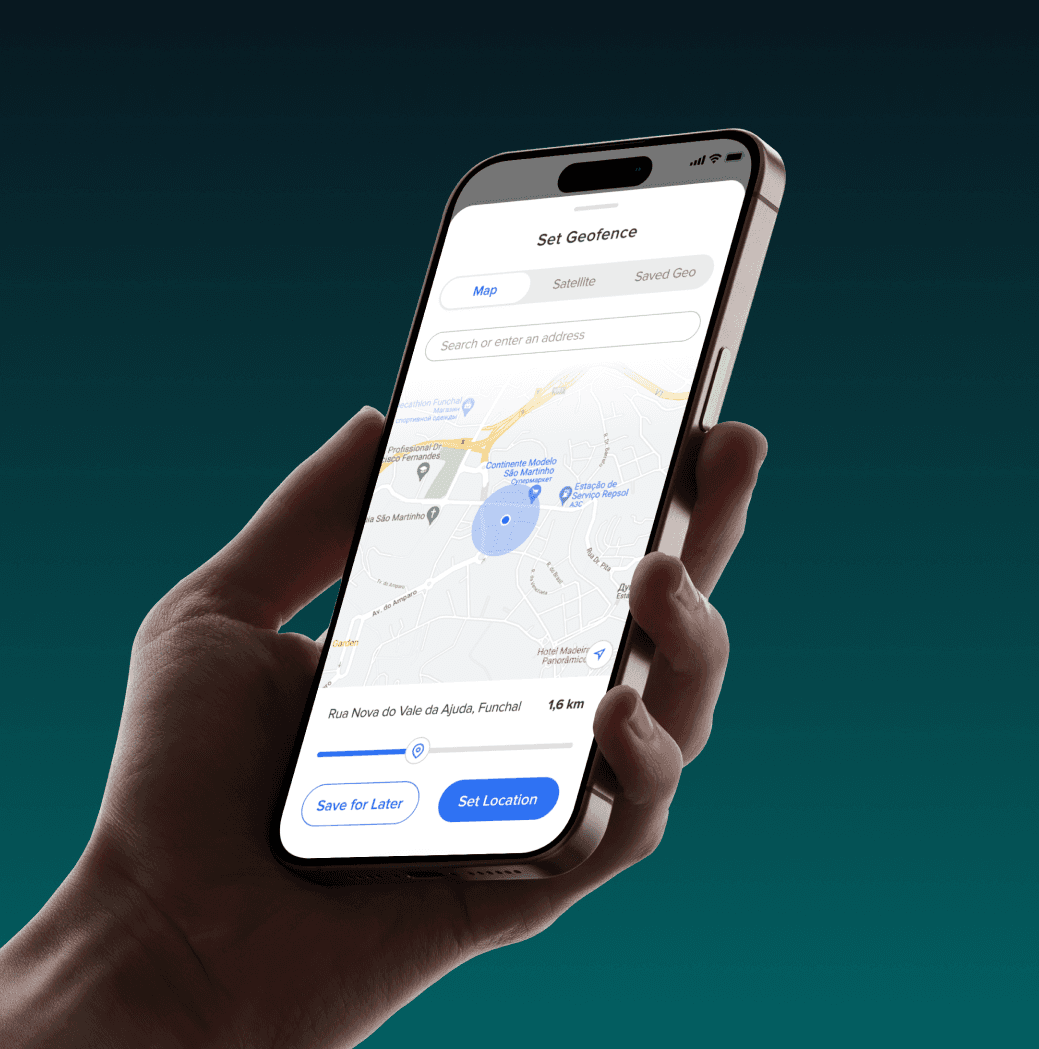
Hardware-Locked Geofencing
Restrict access to specific GPS coordinates (e.g., "Office Only")
Continuous Recognition
Real-time facial monitoring to prevent "shoulder surfing" or unauthorised photos.
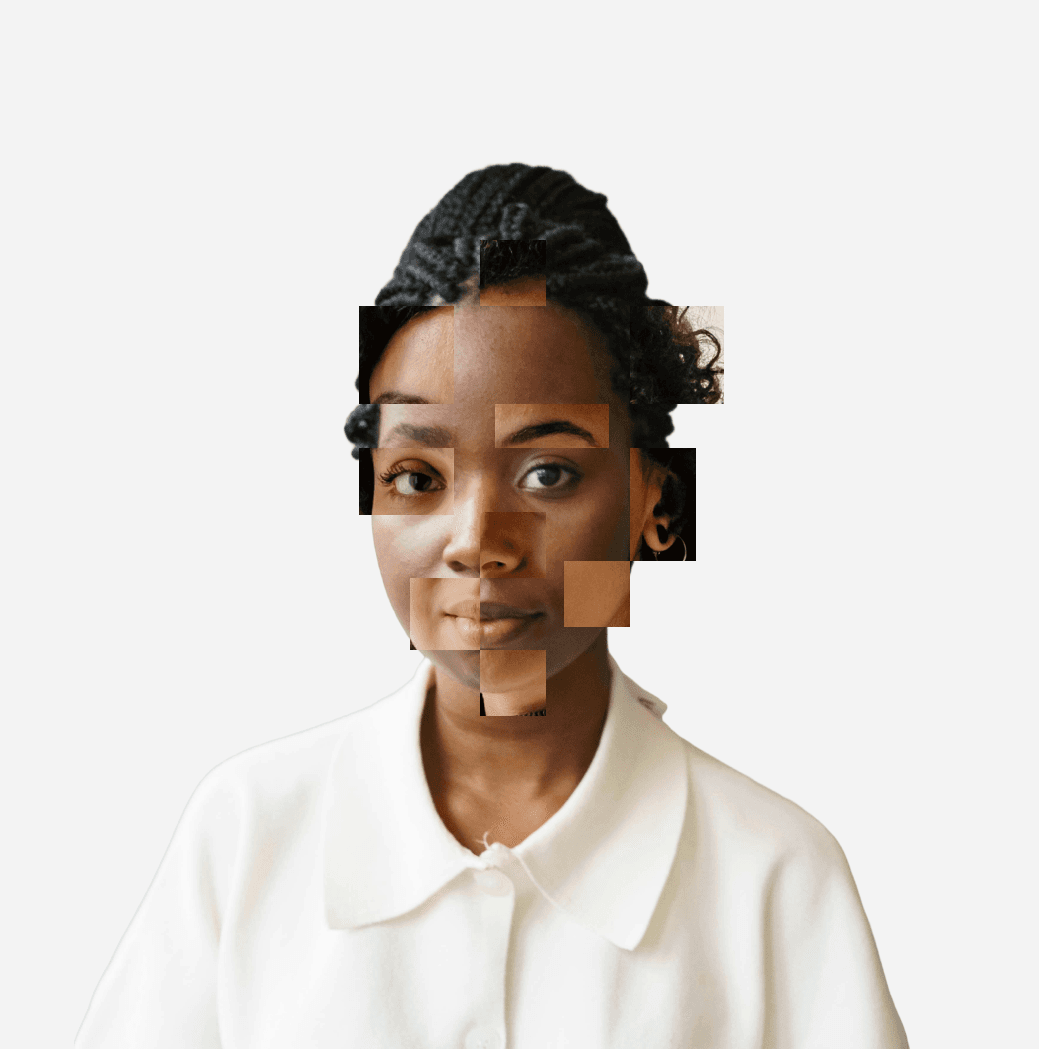
Deepfake Mitigation
Liveness detection ensures the recipient is a real, physical human.

Hard-Coded Recipient Integrity



Evidence of Sight
Biometric confirmation that the intended eyes, and only those eyes, are on the screen.
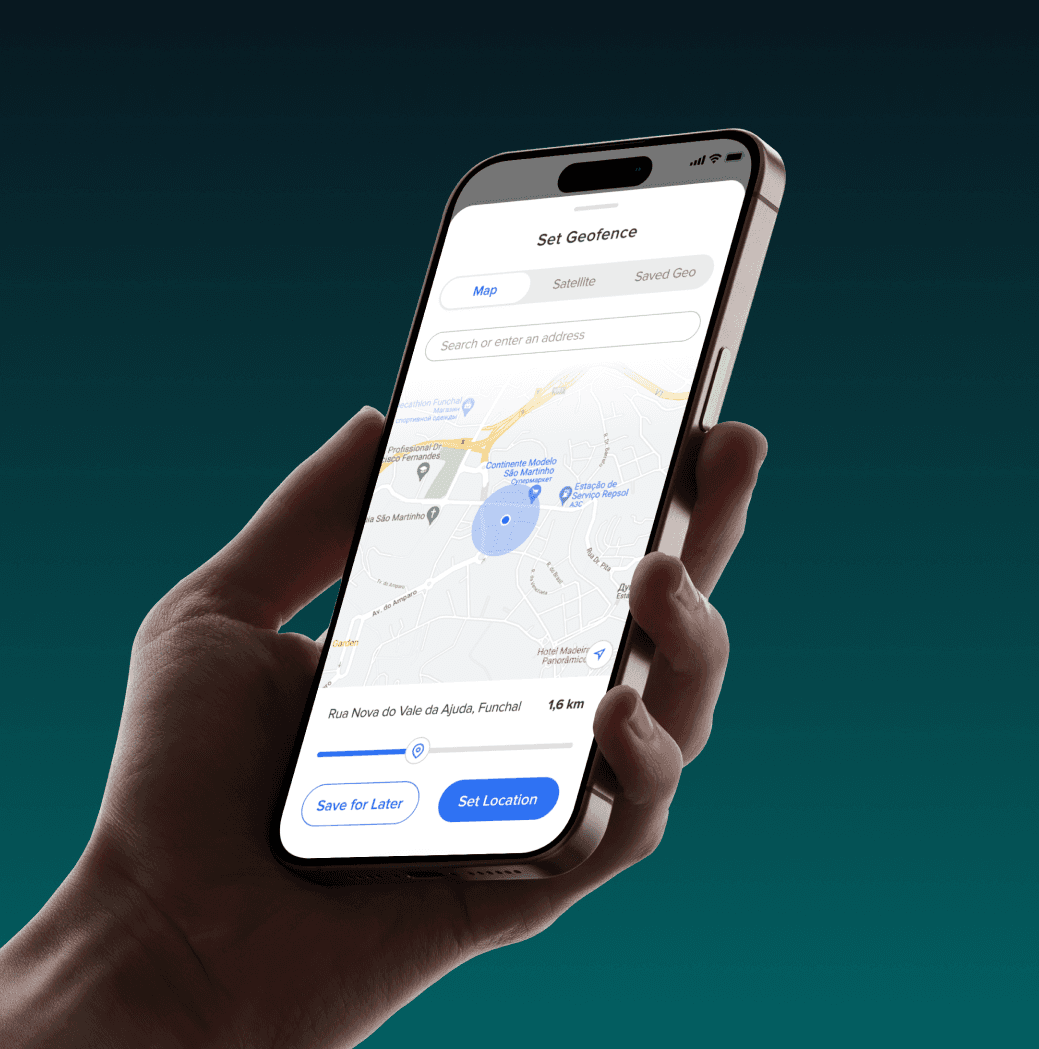
Hardware-Locked Geofencing
Restrict access to specific GPS coordinates (e.g., "Office Only")
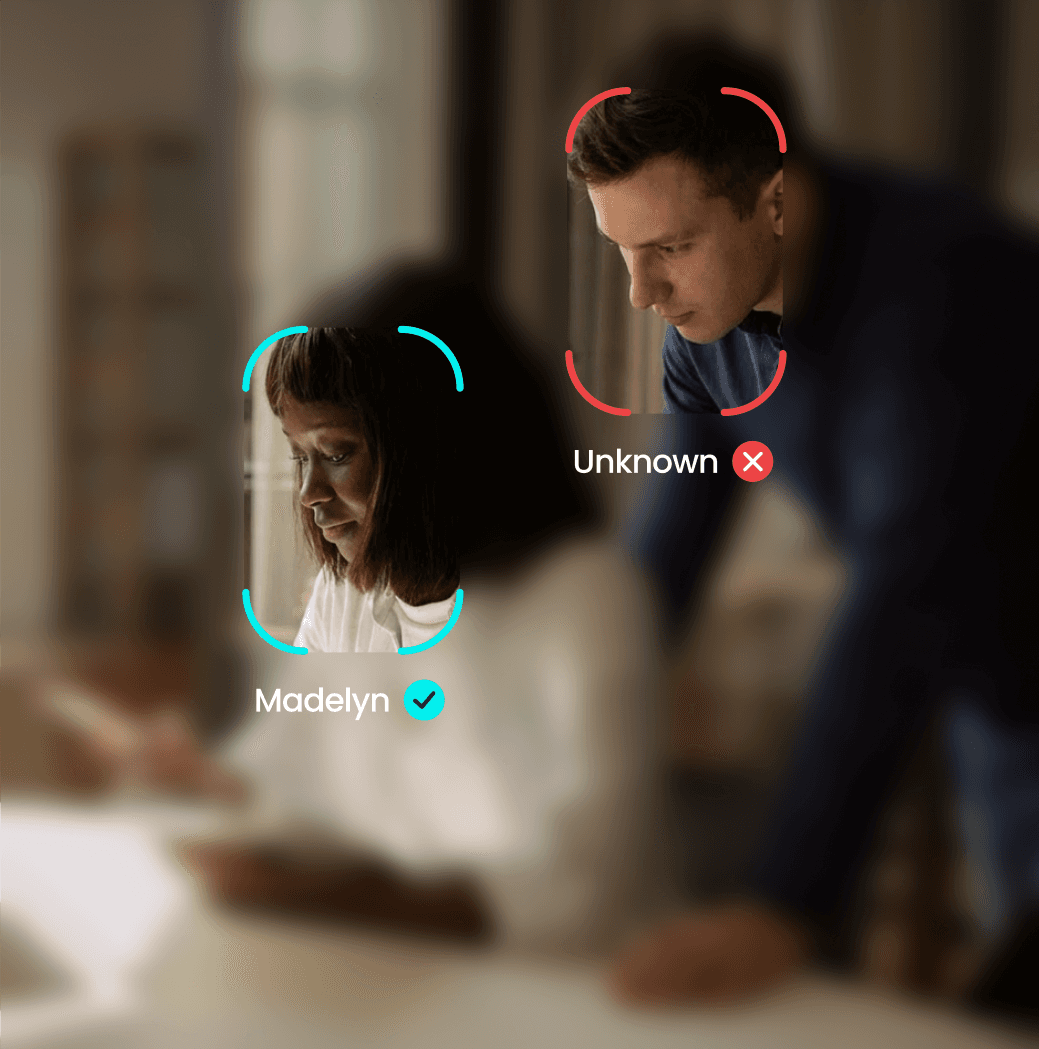
Continuous Recognition
Real-time facial monitoring to prevent "shoulder surfing" or unauthorised photos.
Deepfake Mitigation
Liveness detection ensures the recipient is a real, physical human.

Hard-Coded Recipient Integrity



Evidence of Sight
Biometric confirmation that the intended eyes, and only those eyes, are on the screen.
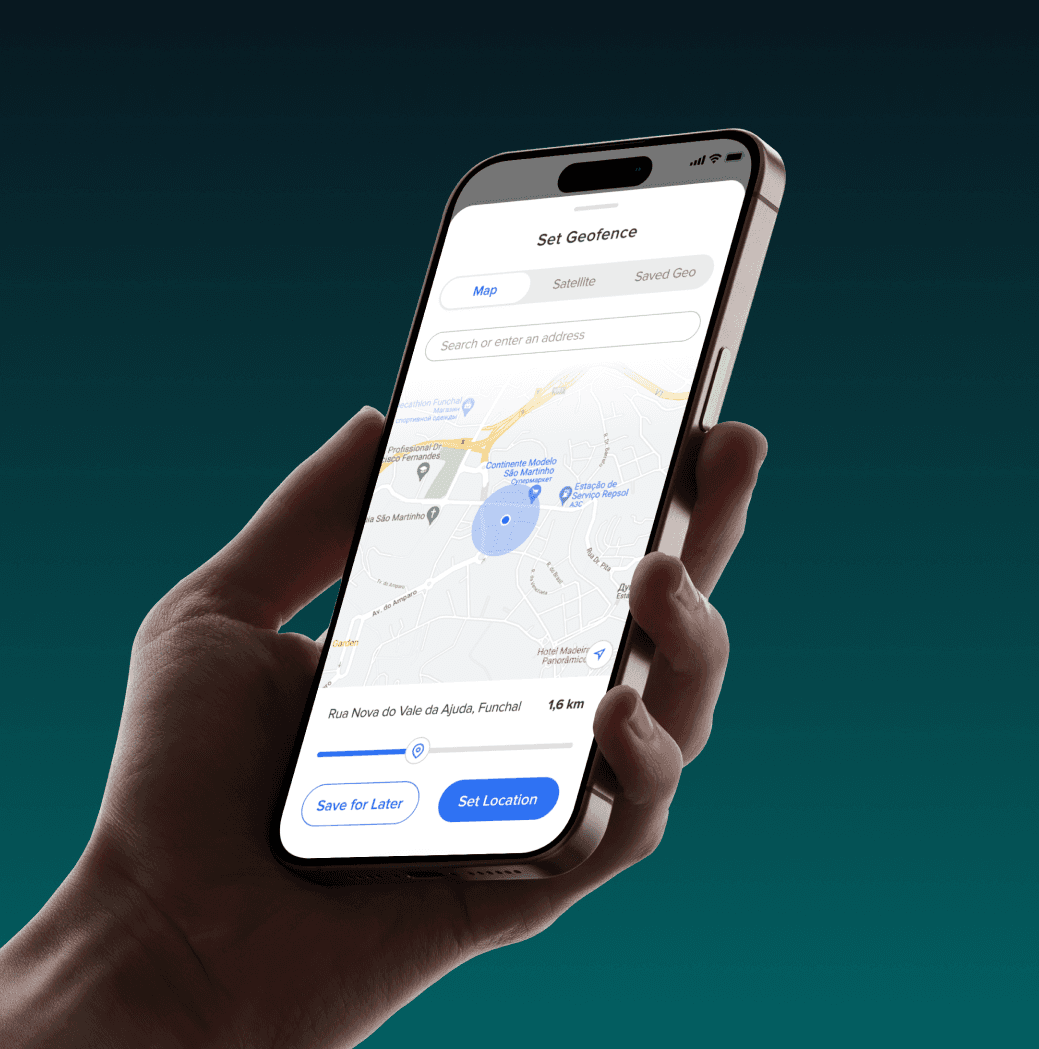
Hardware-Locked Geofencing
Restrict access to specific GPS coordinates (e.g., "Office Only")
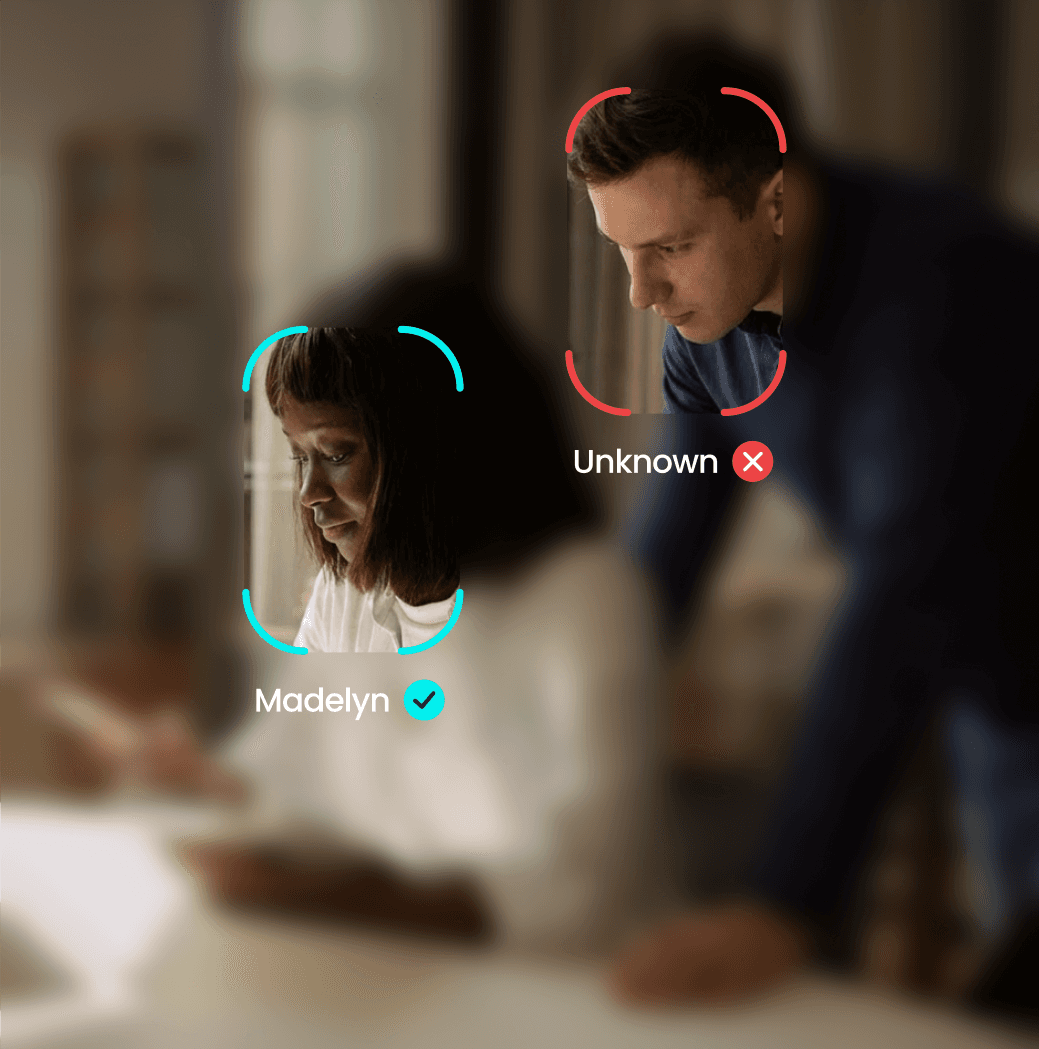
Continuous Recognition
Real-time facial monitoring to prevent "shoulder surfing" or unauthorised photos.
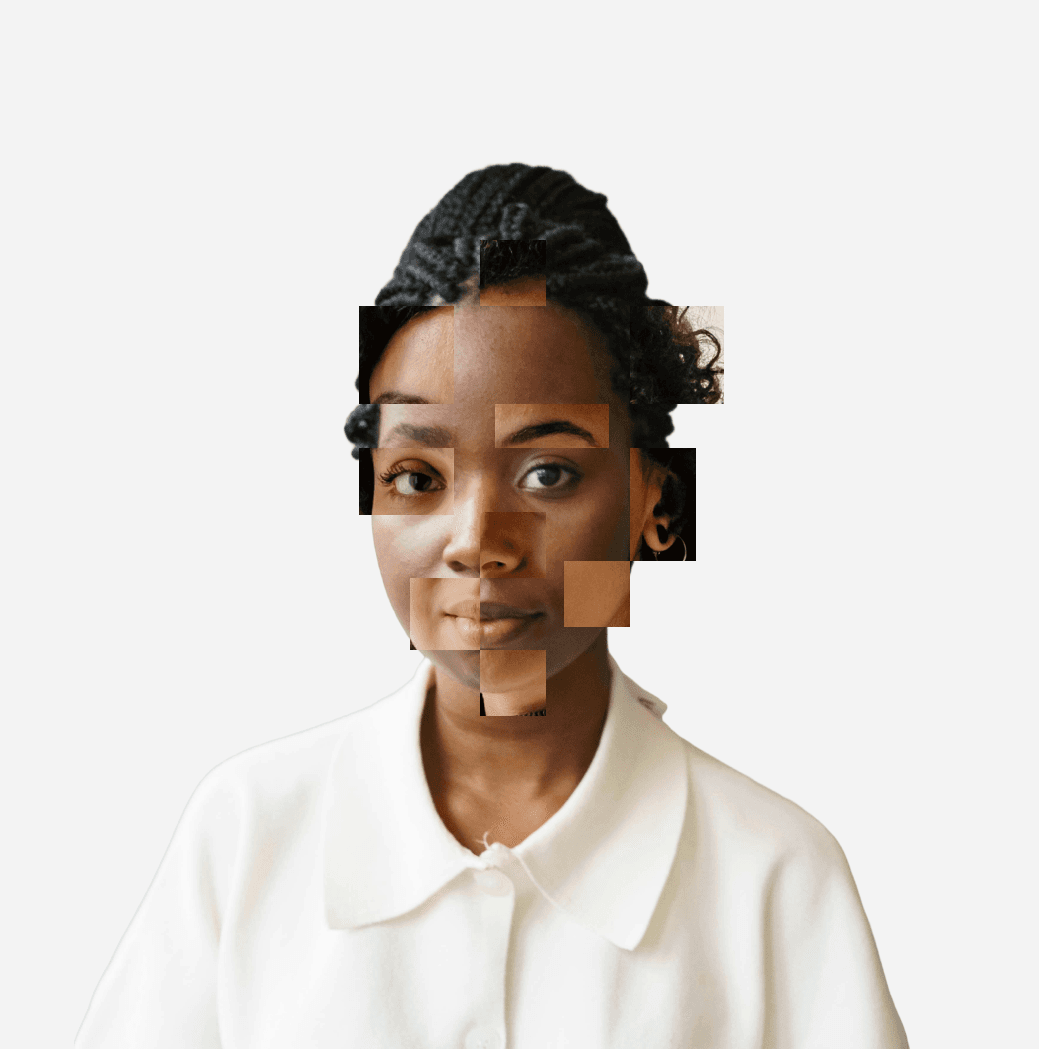
Deepfake Mitigation
Liveness detection ensures the recipient is a real, physical human.
COMPLIANCE
Engineered for Regulatory Rigour
Every confidential file sent without human verification increases exposure under CRB 24-hour disclosure rules.

CRB 24-Hour Filing

SRA Duty of Confidentiality

Professional Indemnity (PII)
COMPLIANCE
Engineered for Regulatory Rigour
Every confidential file sent without human verification increases exposure under CRB 24-hour disclosure rules.

CRB 24-Hour Filing

SRA Duty of Confidentiality

Professional Indemnity (PII)
COMPLIANCE
Engineered for Regulatory Rigour
Every confidential file sent without human verification increases exposure under CRB 24-hour disclosure rules.

CRB 24-Hour Filing

SRA Duty of Confidentiality

Professional Indemnity (PII)

Frequently Asked Questions
Does YEO store biometric data?
What happens if facial recognition fails?
Can it run on unmanaged devices?
Is the verification process intrusive for lawyers?


Stop Researching. Start Verifying.
Own the Evidence of Sight. Download the full Technical Matrix to see how YEO integrates into your firm’s security stack.


Stop Researching. Start Verifying.
Own the Evidence of Sight. Download the full Technical Matrix to see how YEO integrates into your firm’s security stack.


Stop Researching. Start Verifying.
Own the Evidence of Sight. Download the full Technical Matrix to see how YEO integrates into your firm’s security stack.





