
Continuous Human Verification for Security Teams
Don’t Just Report a Breach: Prove Who Saw the Data.
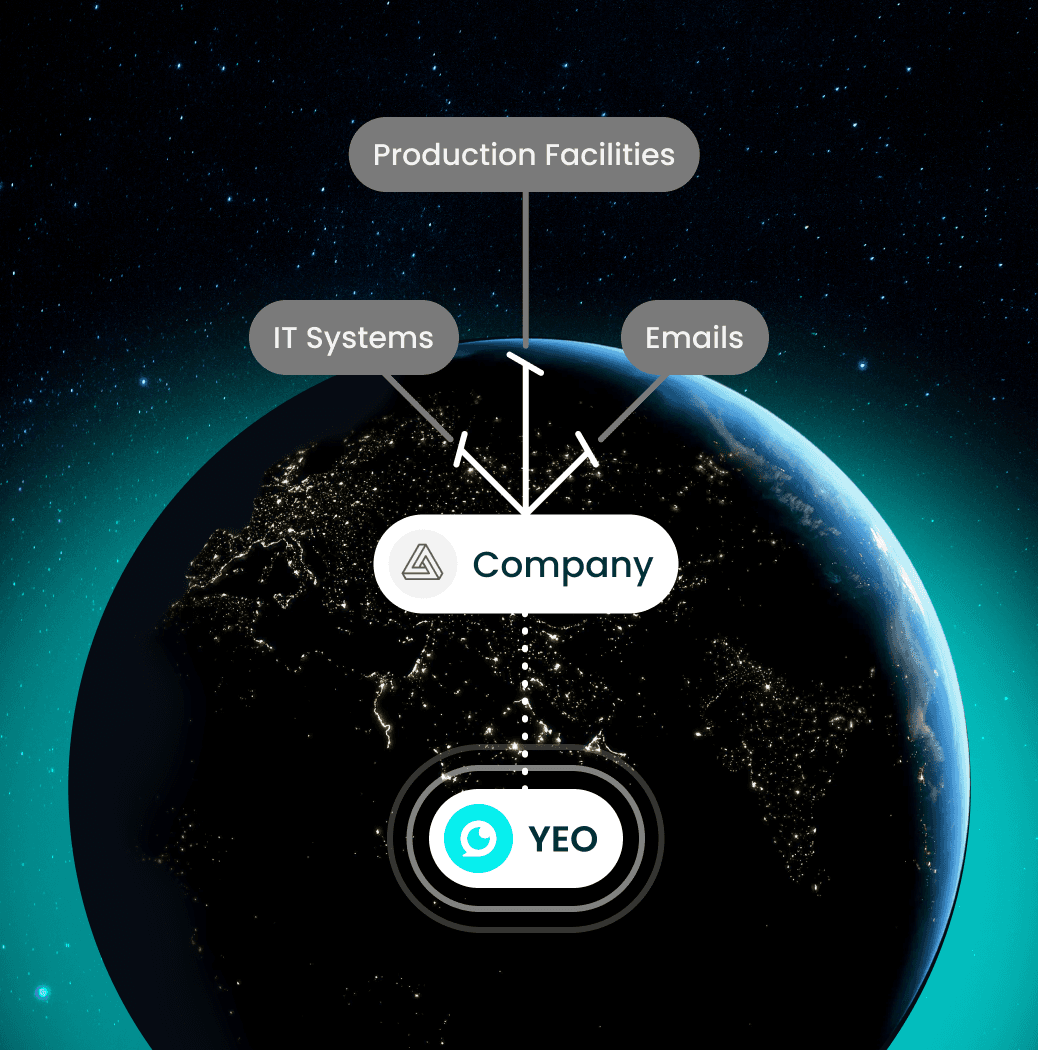
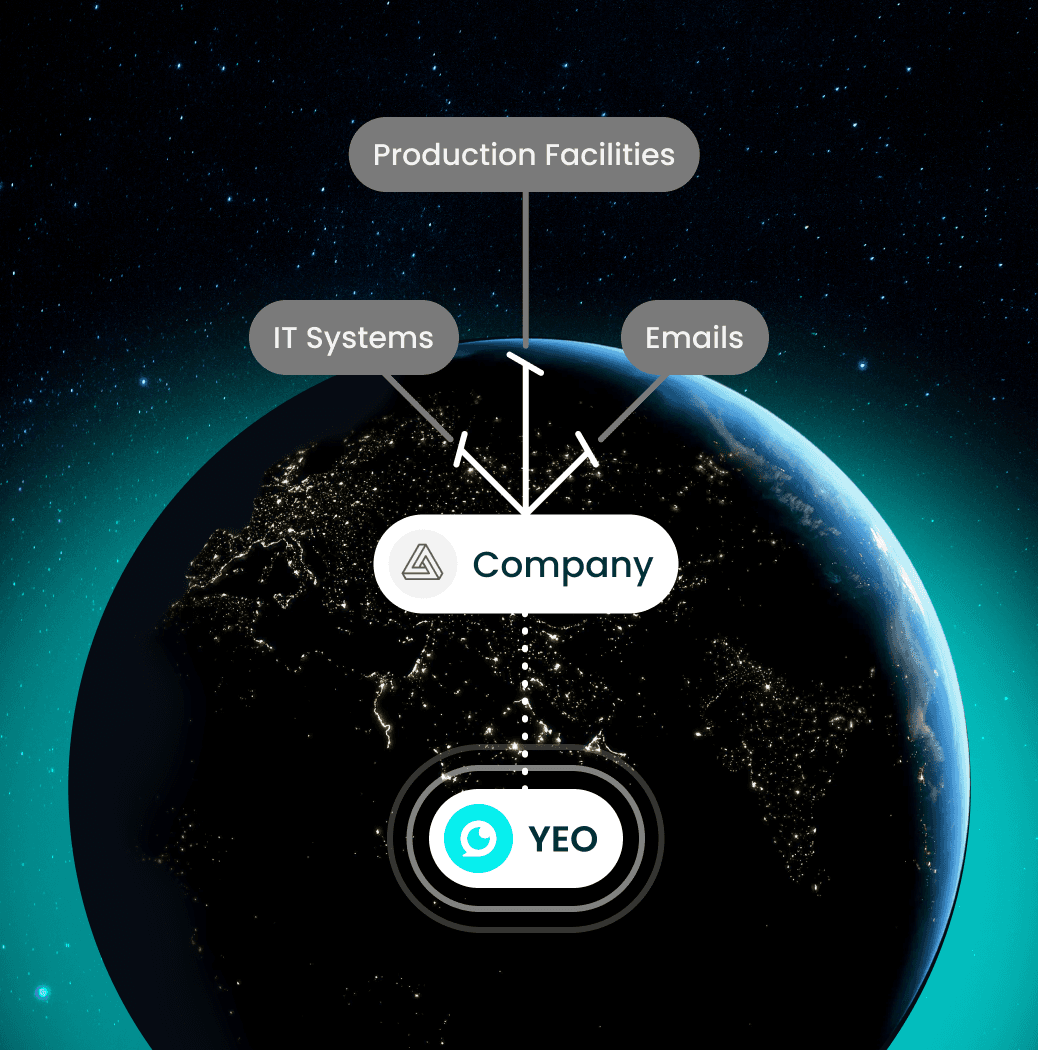
YEO adds an independent out-of-band (OOB) verification channel that confirms the right human is present throughout the session: producing defensible Evidence of Sight for CRB-compliant audit trails.


Don’t Just Report a Breach: Prove Who Saw the Data.
YEO adds an independent out-of-band (OOB) verification channel that confirms the right human is present throughout the session: producing defensible Evidence of Sight for CRB-compliant audit trails.


Continuous Human Verification for Security Teams
Don’t Just Report a Breach: Prove Who Saw the Data.
YEO adds an independent out-of-band (OOB) verification channel that confirms the right human is present throughout the session: producing defensible Evidence of Sight for CRB-compliant audit trails.



















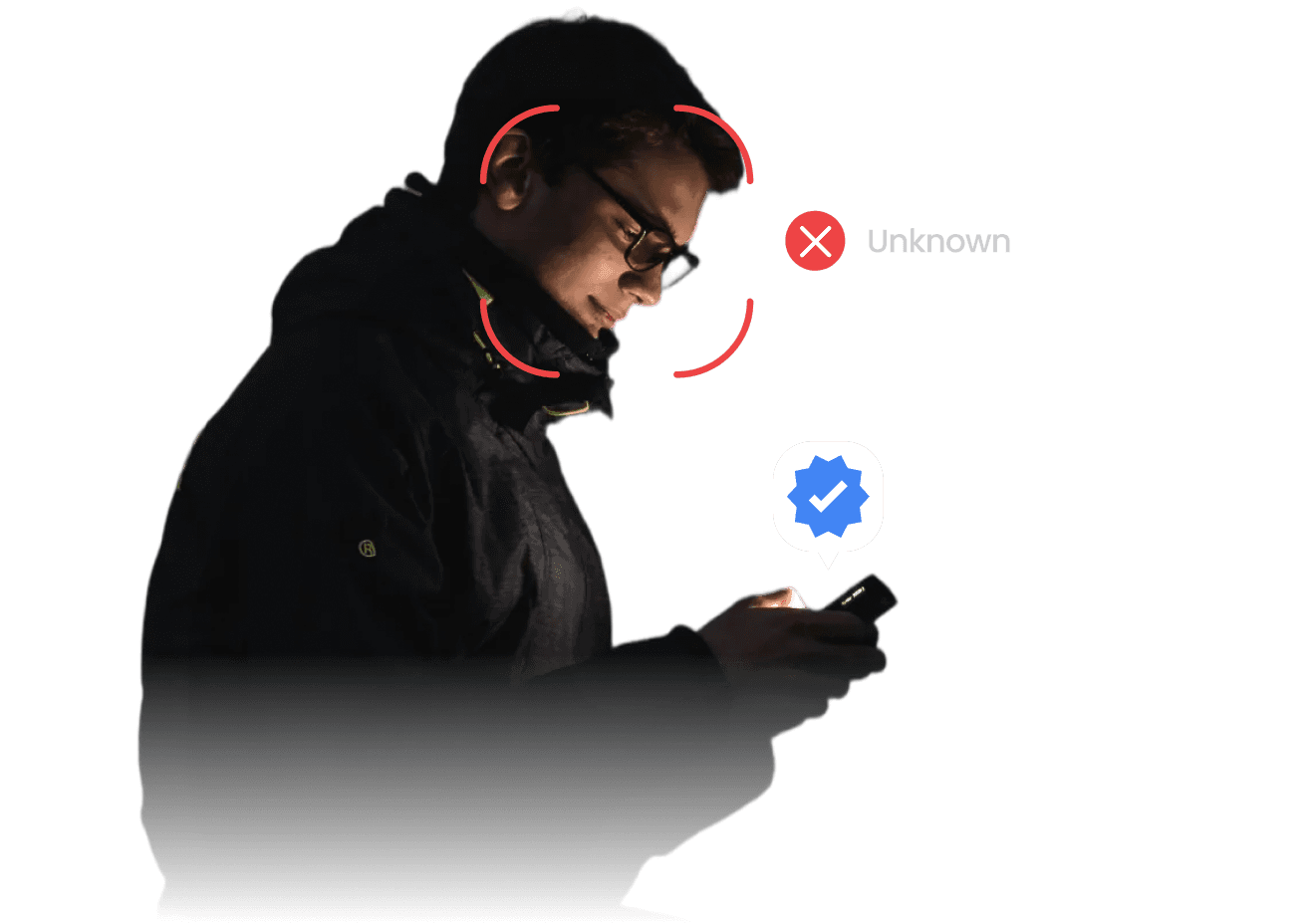
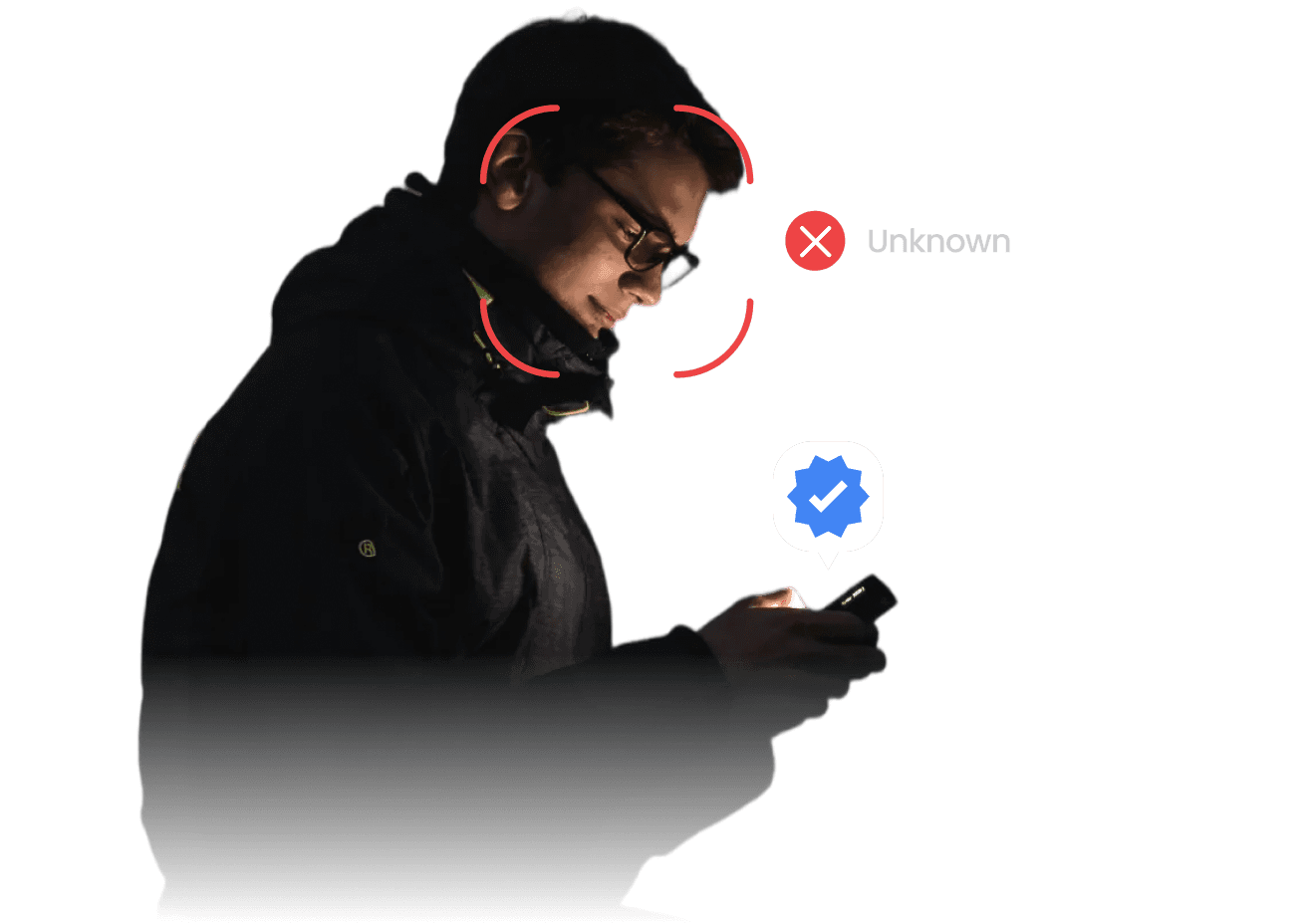
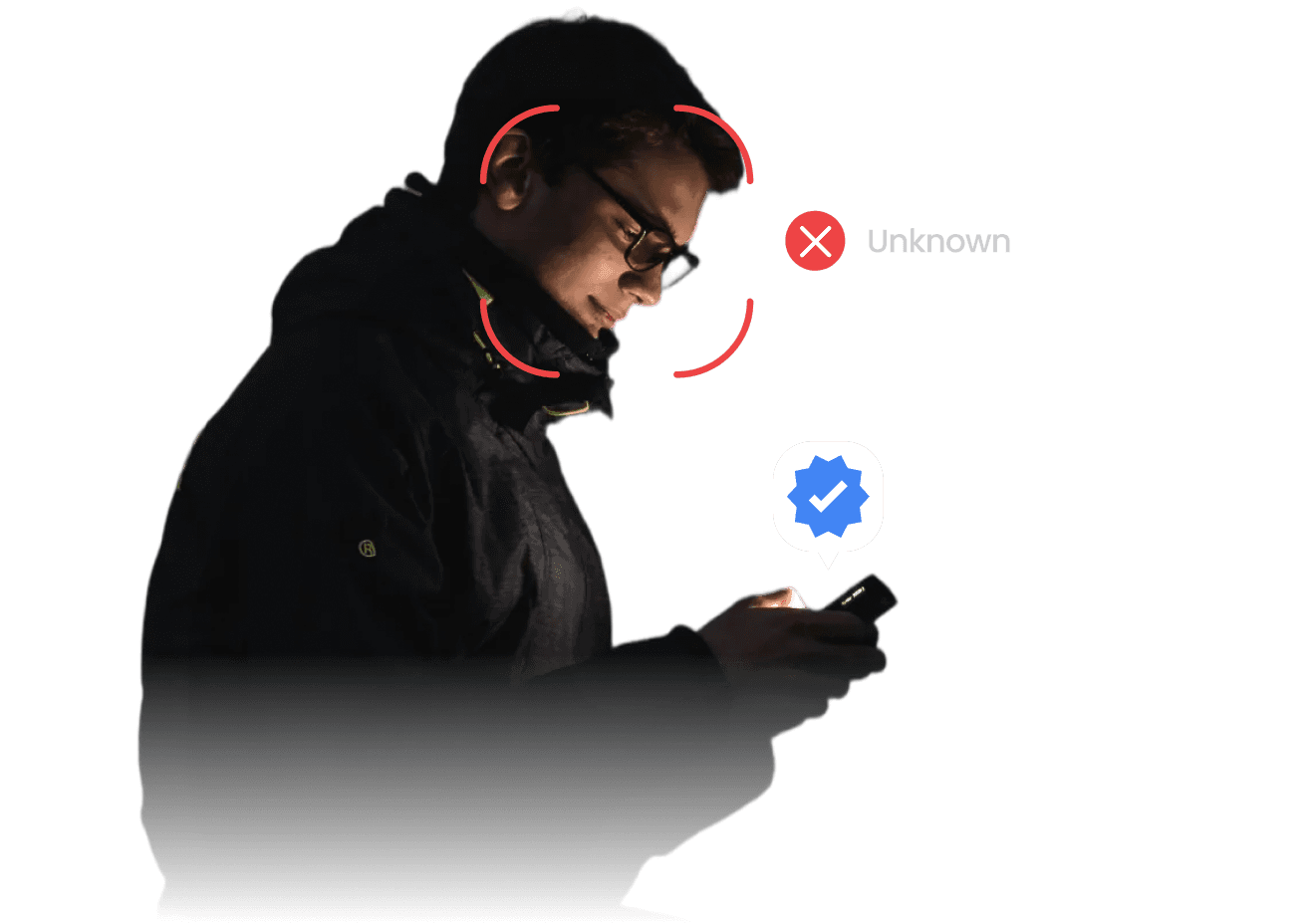
Authentication is a moment. Recipient integrity must be continuous.
Authentication is a moment. Recipient integrity must be continuous.
Authentication is a moment. Recipient integrity must be continuous.
THE PROBLEM
Why Device-Level MFA Fails the Human Test
Your perimeter is only as secure as the person actually viewing the data at the terminal.

THE PROBLEM
Why Device-Level MFA Fails the Human Test
Your perimeter is only as secure as the person actually viewing the data at the terminal.

THE PROBLEM
Why Device-Level MFA Fails the Human Test
Your perimeter is only as secure as the person actually viewing the data at the terminal.

CRB Regulatory Warning
Regulators no longer accept ‘sent’ as proof. 24-hour filing requirements demand immutable proof of who consumed the data.
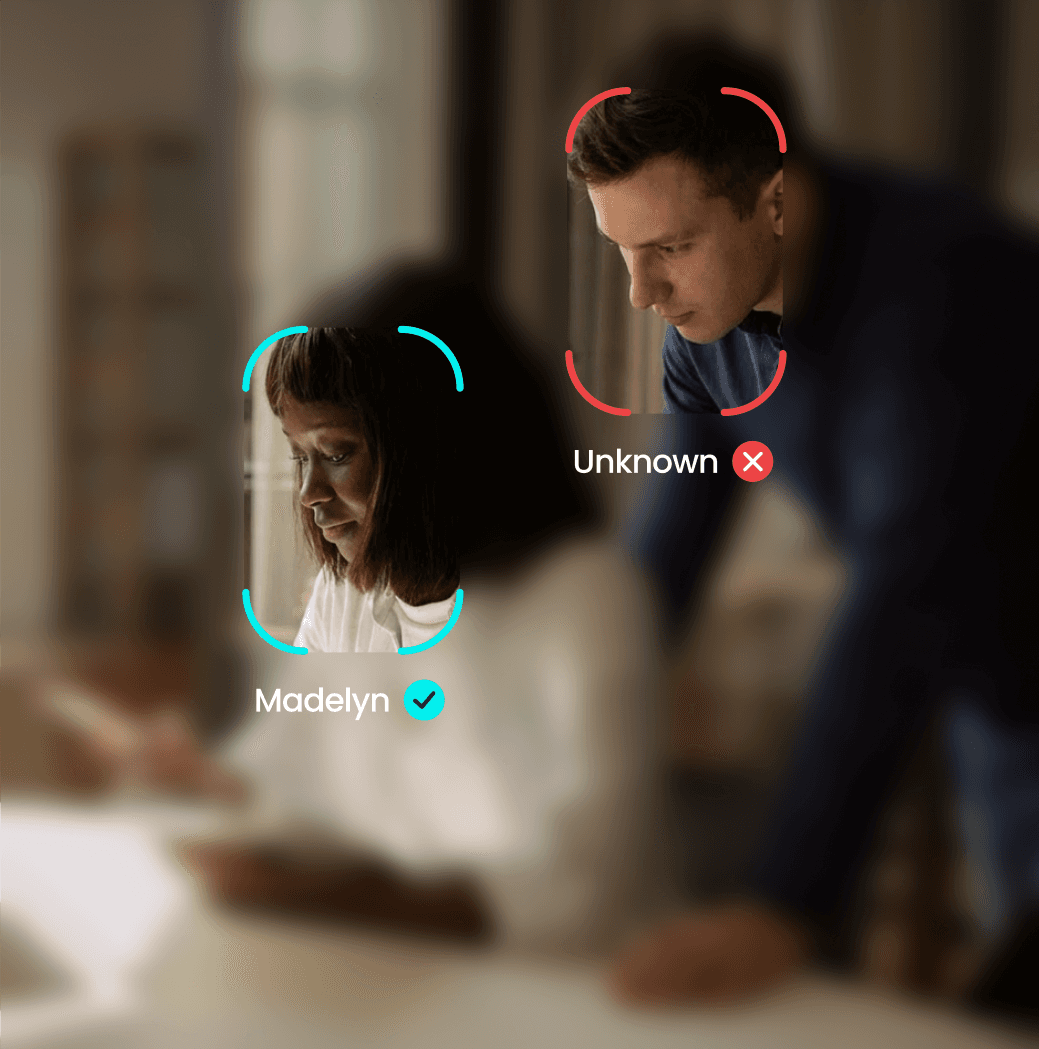
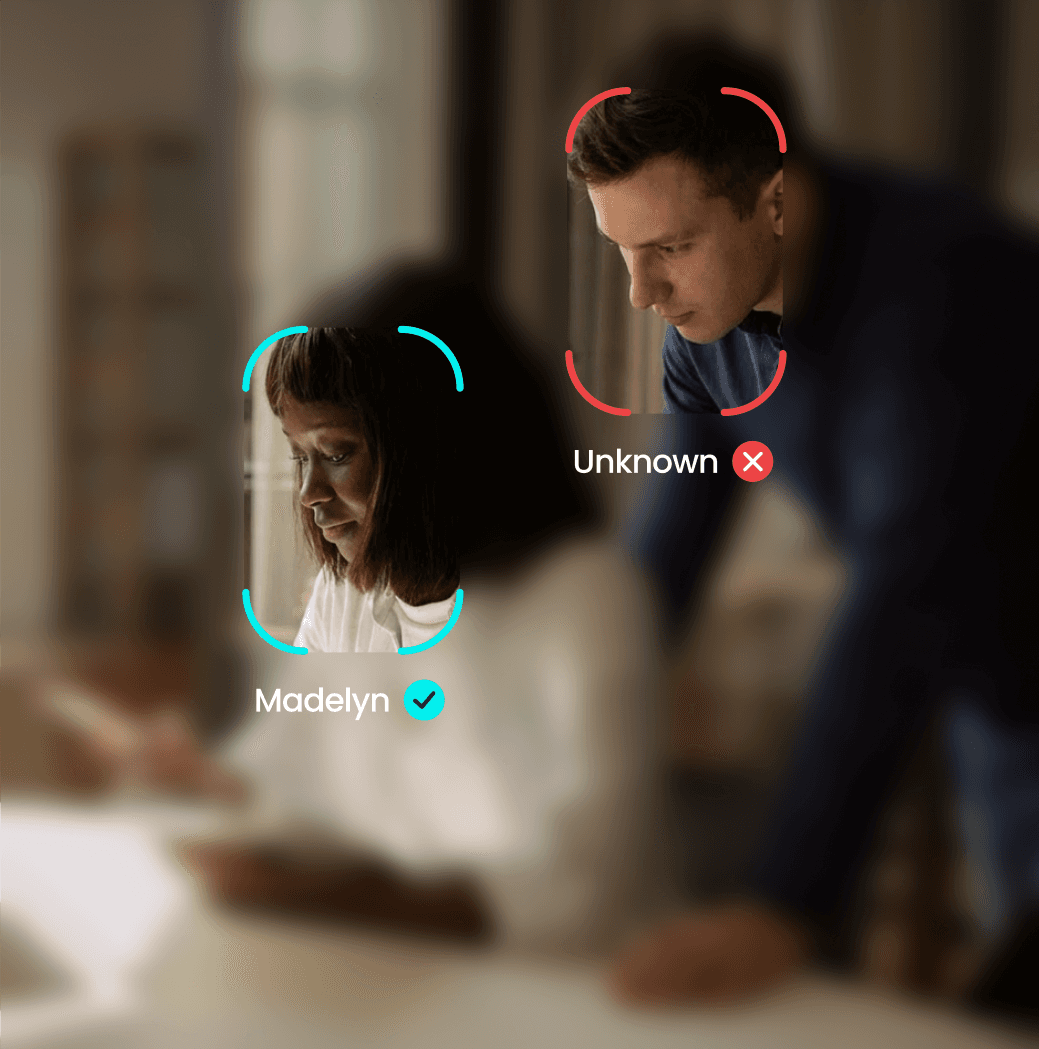
The Post-Login Blindspot
Standard MFA stops at the "door." YEO monitors the "room," ensuring the human remains the authorised recipient throughout the session.
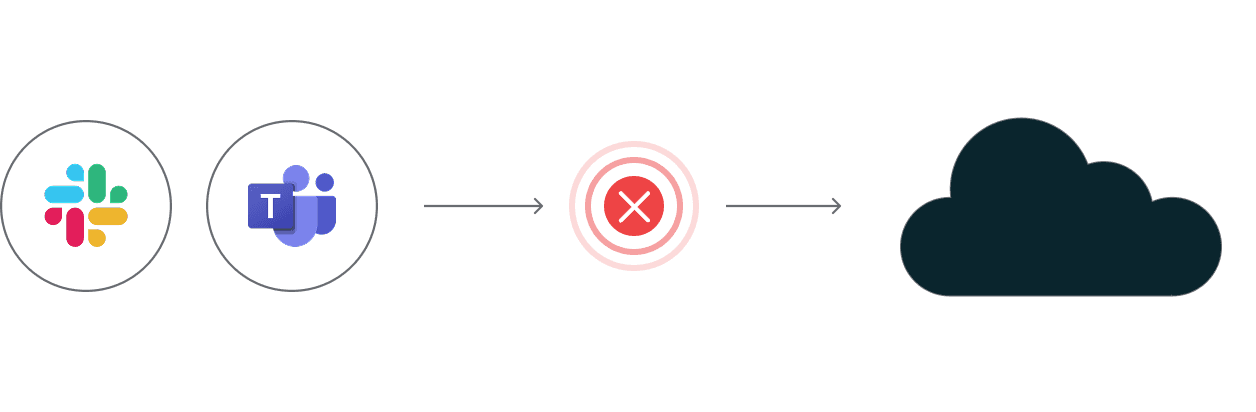
In-Band Vulnerability
When primary infrastructure is compromised, "In-Band" tokens (SMS/App push) are equally vulnerable to interception.
The Forensic Deficit
"Successfully Delivered" is not a legal proof of receipt. You need tamper-evident Evidence of Sight for regulatory filing.

CRB Regulatory Warning
Regulators no longer accept ‘sent’ as proof. 24-hour filing requirements demand immutable proof of who consumed the data.
The Post-Login Blindspot
Standard MFA stops at the "door." YEO monitors the "room," ensuring the human remains the authorised recipient throughout the session.
In-Band Vulnerability
When primary infrastructure is compromised, "In-Band" tokens (SMS/App push) are equally vulnerable to interception.
The Forensic Deficit
"Successfully Delivered" is not a legal proof of receipt. You need tamper-evident Evidence of Sight for regulatory filing.

CRB Regulatory Warning
Regulators no longer accept ‘sent’ as proof. 24-hour filing requirements demand immutable proof of who consumed the data.
The Post-Login Blindspot
Standard MFA stops at the "door." YEO monitors the "room," ensuring the human remains the authorised recipient throughout the session.
In-Band Vulnerability
When primary infrastructure is compromised, "In-Band" tokens (SMS/App push) are equally vulnerable to interception.
The Forensic Deficit
"Successfully Delivered" is not a legal proof of receipt. You need tamper-evident Evidence of Sight for regulatory filing.

Compare YEO with Legacy Infrastructure
YEO
Standard MFA
Out-of-Band Architecture
Continuous Biometric Verification
Hardware-Locked Geofencing
CRB-Ready Audit Trails
Deepfake Mitigation
Compare YEO with Legacy Infrastructure
YEO
Standard MFA
Out-of-Band Architecture
Continuous Biometric Verification
Hardware-Locked Geofencing
CRB-Ready Audit Trails
Deepfake Mitigation
Compare YEO with Legacy Infrastructure
YEO
Standard MFA
Out-of-Band Architecture
Continuous Biometric Verification
Hardware-Locked Geofencing
CRB-Ready Audit Trails
Deepfake Mitigation
Engineered for Architectural Resilience
Bypassing compromised infrastructure to establish a direct, independent link to the verified human user.

Primary Network Failure
Infrastructure is compromised or under active attack.
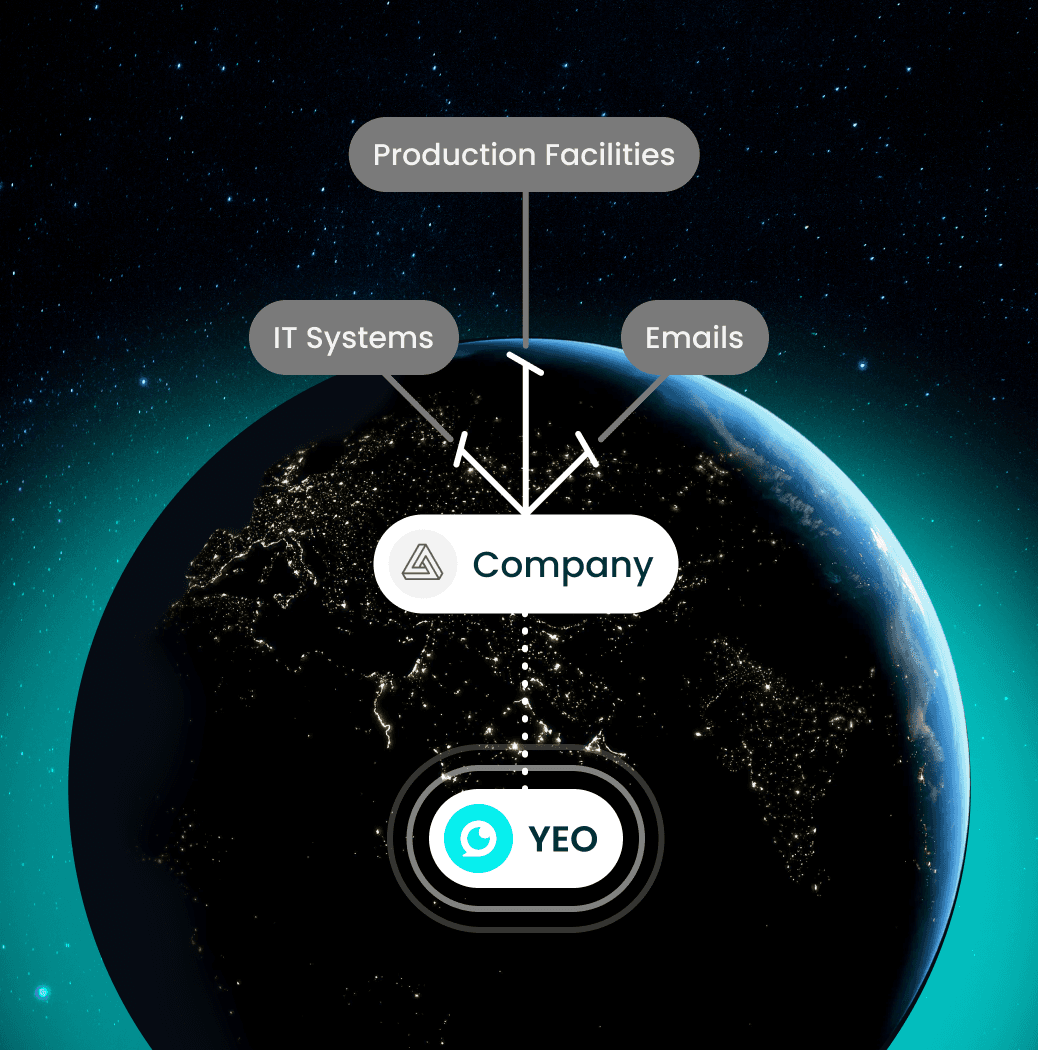
OOB Handshake
YEO establishes an independent, air-gapped authentication path via the YEO OOB platform.
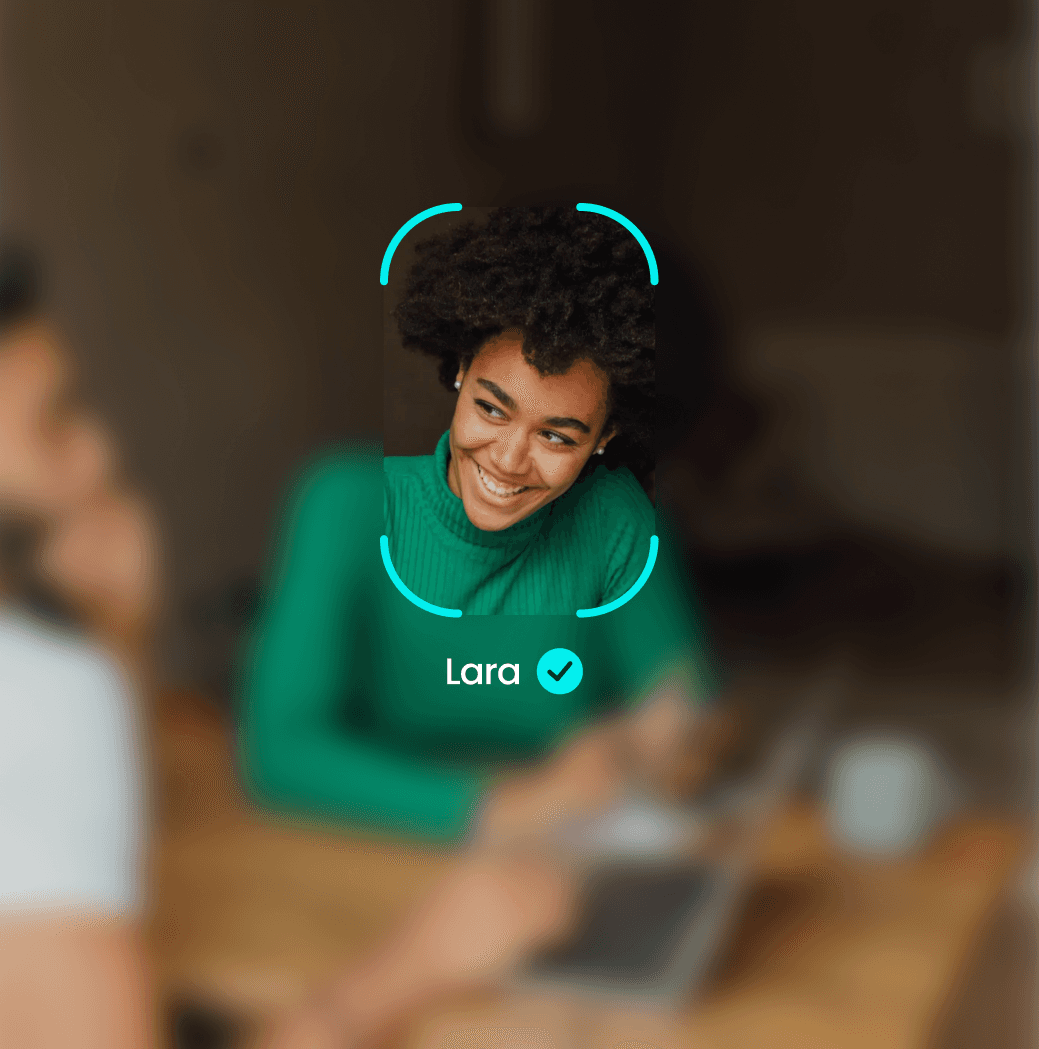
Continuous Biometric Hook
Face-locked liveness detection ensures the human is present throughout the viewing session.

Immutable Evidence
Tamper-evident, time-stamped event logs with exportable metadata generated instantly for filing.
STEP 1
Attack Detected
STEP 2
Activate YEO
STEP 3
Verify & Connect
STEP 4
Coordinate Response
Engineered for Architectural Resilience
Bypassing compromised infrastructure to establish a direct, independent link to the verified human user.

Primary Network Failure
Infrastructure is compromised or under active attack.
OOB Handshake
YEO establishes an independent, air-gapped authentication path via the YEO OOB platform.
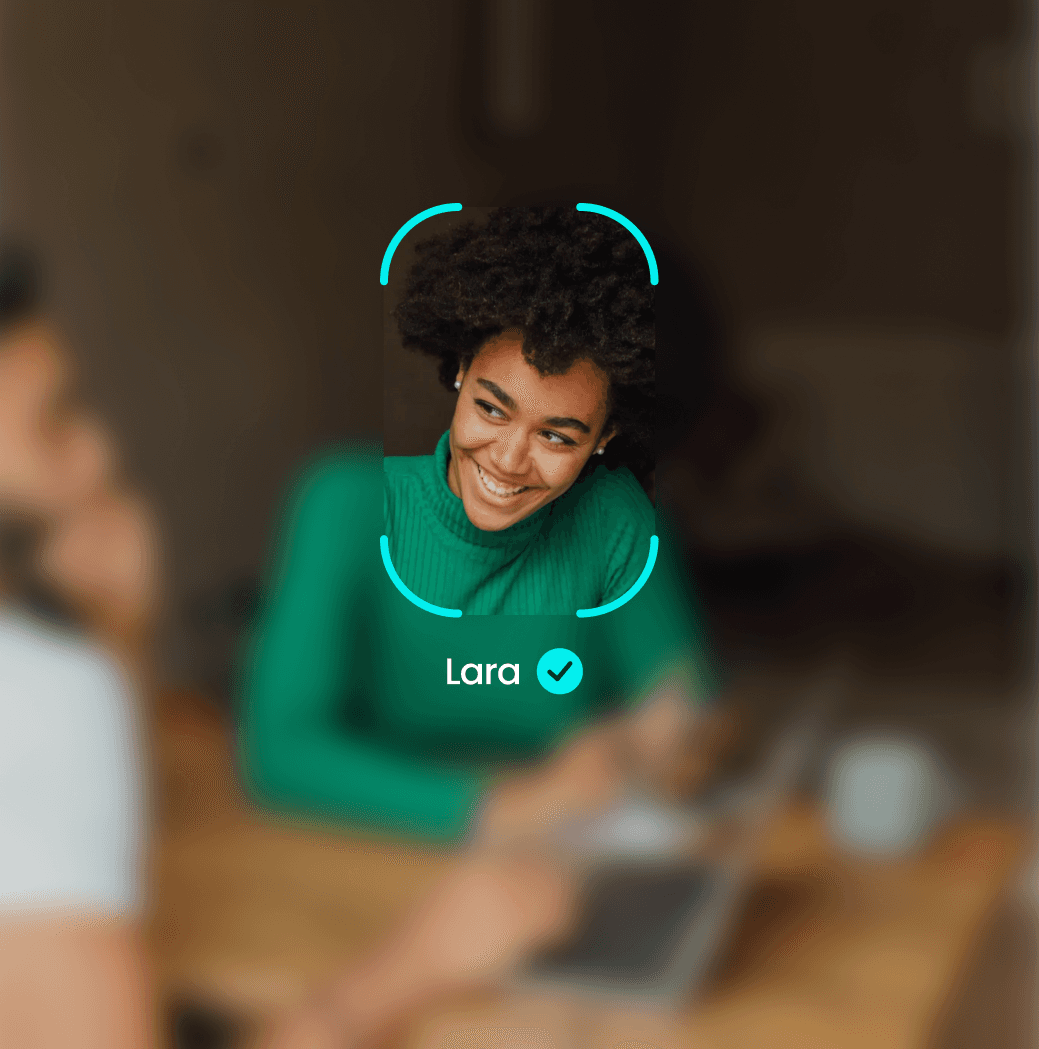
Continuous Biometric Hook
Face-locked liveness detection ensures the human is present throughout the viewing session.

Immutable Evidence
Tamper-evident, time-stamped event logs with exportable metadata generated instantly for filing.
STEP 1
Attack Detected
STEP 2
Activate YEO
STEP 3
Verify & Connect
STEP 4
Coordinate Response
Engineered for Architectural Resilience
Bypassing compromised infrastructure to establish a direct, independent link to the verified human user.

Primary Network Failure
Infrastructure is compromised or under active attack.
OOB Handshake
YEO establishes an independent, air-gapped authentication path via the YEO OOB platform.
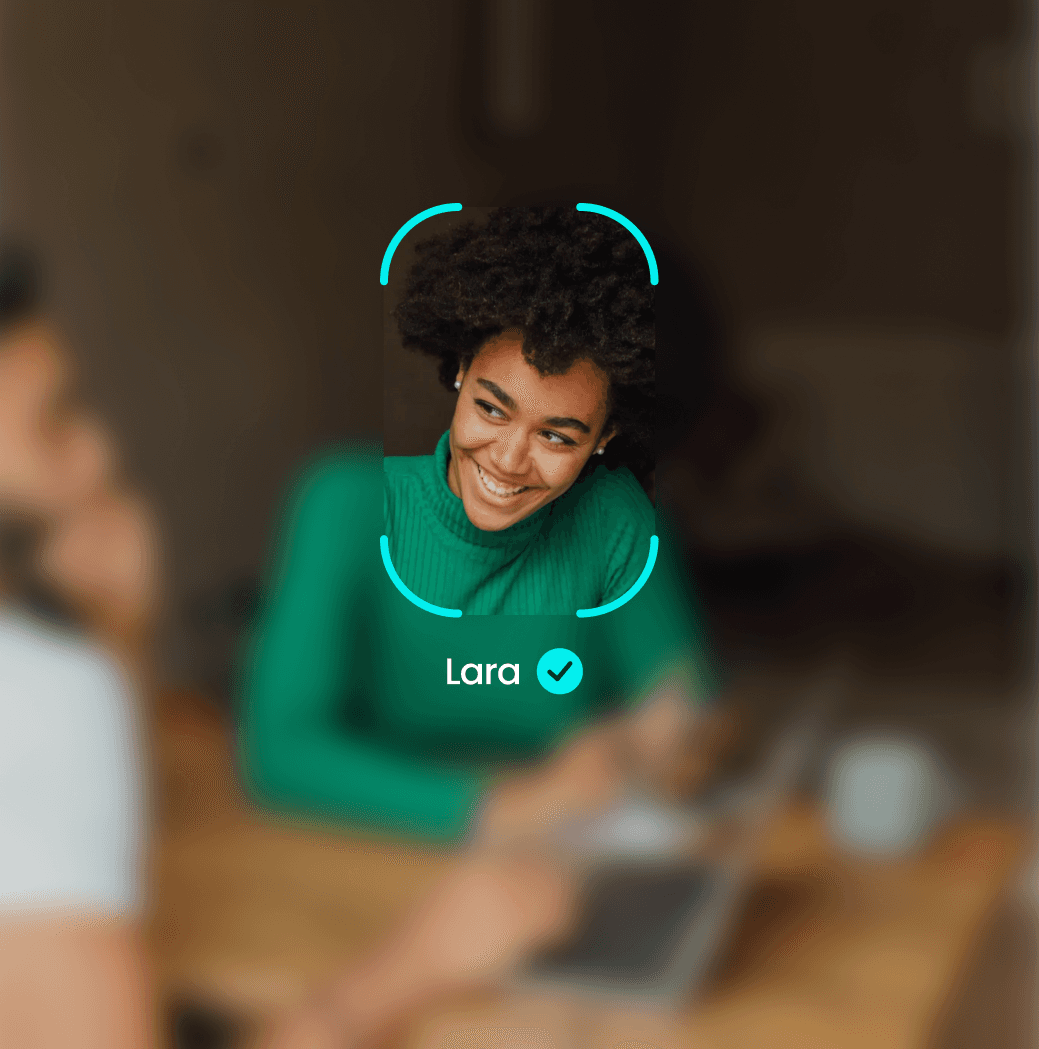
Continuous Biometric Hook
Face-locked liveness detection ensures the human is present throughout the viewing session.

Immutable Evidence
Tamper-evident, time-stamped event logs with exportable metadata generated instantly for filing.
STEP 1
Attack Detected
STEP 2
Activate YEO
STEP 3
Verify & Connect
STEP 4
Coordinate Response
Enterprise-Grade Verification. Minimal Workflow Change.
YEO isn't just about secure communication—it’s about creating a trusted, compliant, and resilient incident response capability when everything else is compromised.
Privacy First
No sensitive message content is required for proof generation.
Controlled Pilot
Deploy as a targeted pilot for a single team or high-risk workflow before full rollout.
Rapid Reporting
Audit outputs designed for immediate SIEM/Forensic review.
OOB Resilience
Physically separate from your network
Continuous Identity Assurance
Users are continuously verified during sensitive communications
Stack Integration
Works alongside your existing MFA and Identity Provider (IdP) stack.

Enterprise-Grade Verification. Minimal Workflow Change.
YEO isn't just about secure communication—it’s about creating a trusted, compliant, and resilient incident response capability when everything else is compromised.
Privacy First
No sensitive message content is required for proof generation.
Controlled Pilot
Deploy as a targeted pilot for a single team or high-risk workflow before full rollout.
Rapid Reporting
Audit outputs designed for immediate SIEM/Forensic review.
OOB Resilience
Physically separate from your network
Continuous Identity Assurance
Users are continuously verified during sensitive communications
Stack Integration
Works alongside your existing MFA and Identity Provider (IdP) stack.


Hard-Coded Recipient Integrity



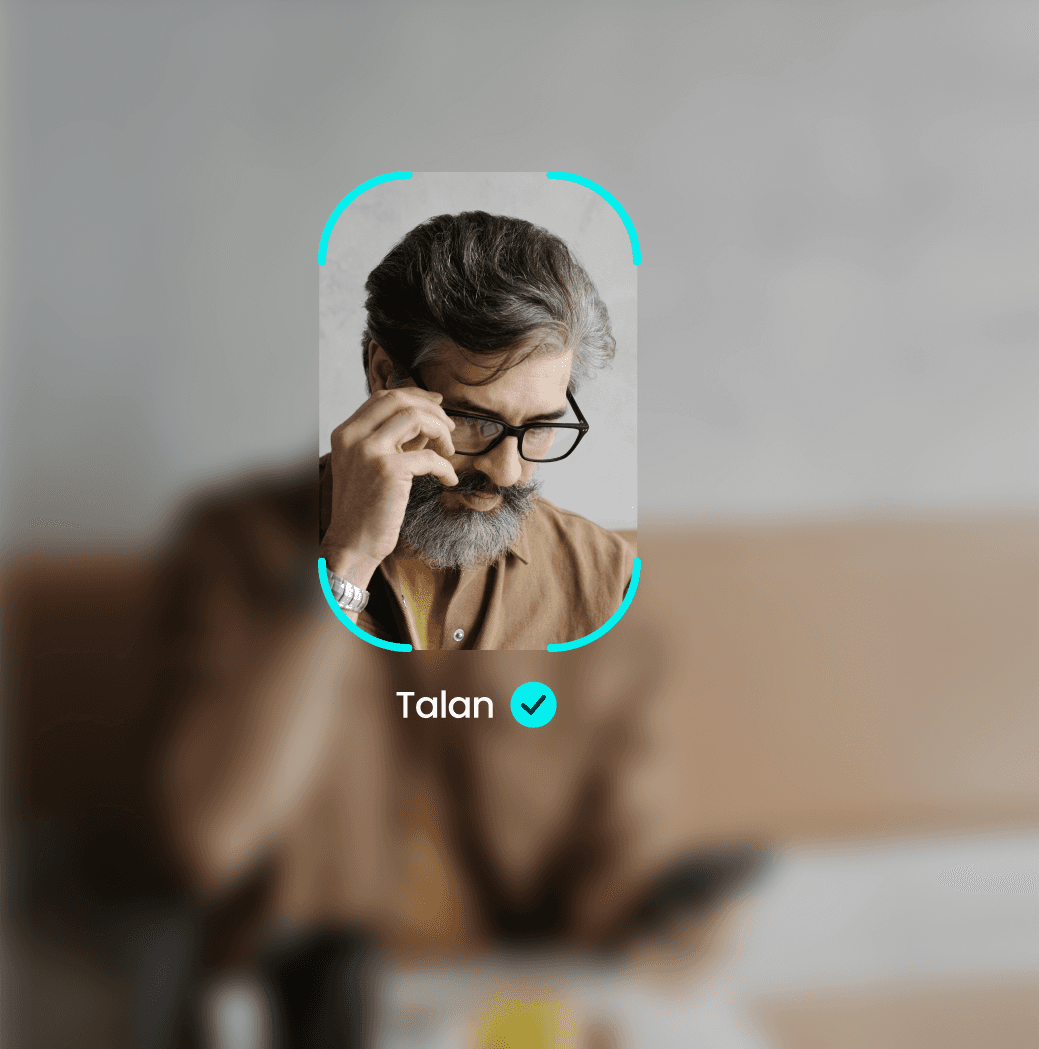
Evidence of Sight
Biometric confirmation that the intended eyes, and only those eyes, are on the screen.
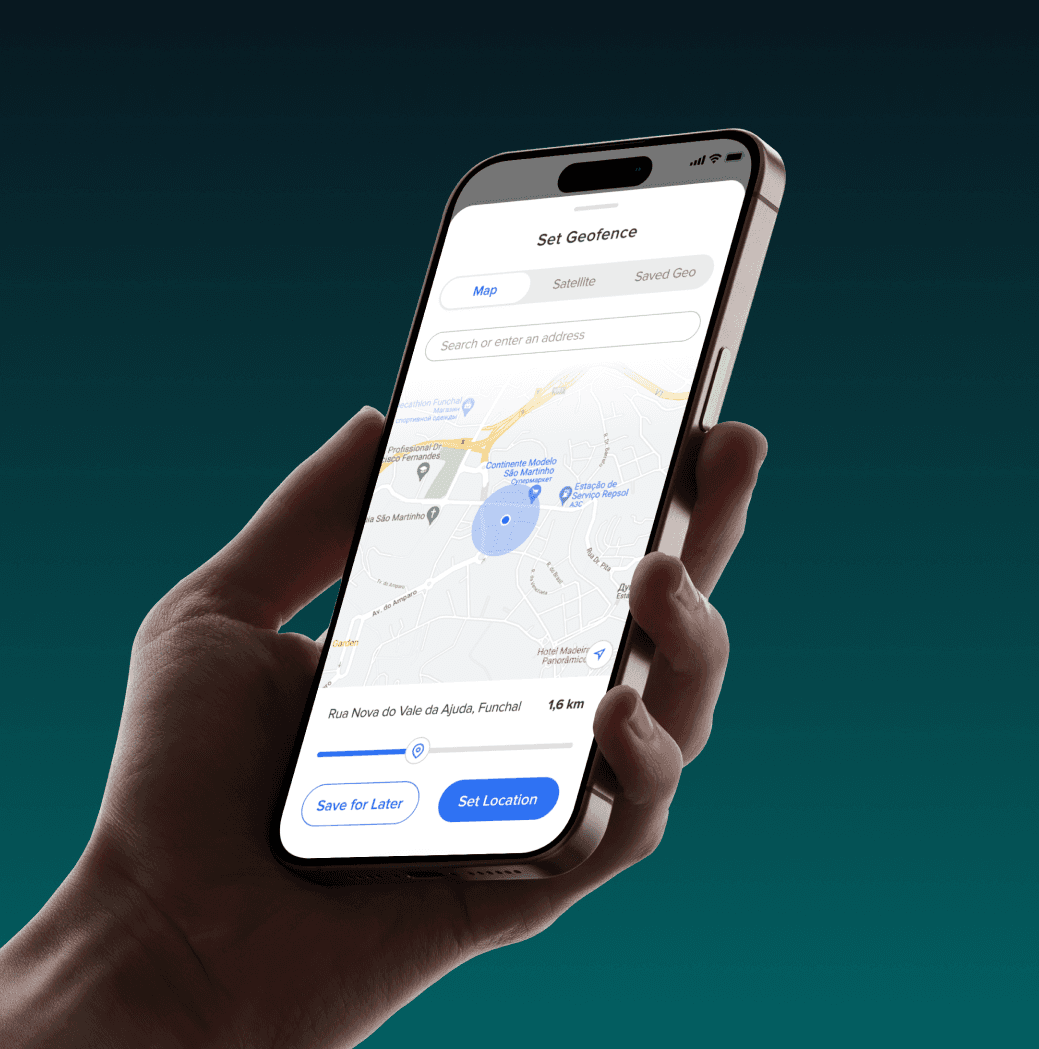
Hardware-Locked Geofencing
Precise, GPS-locked access boundaries ensuring sensitive data stays within authorised zones.
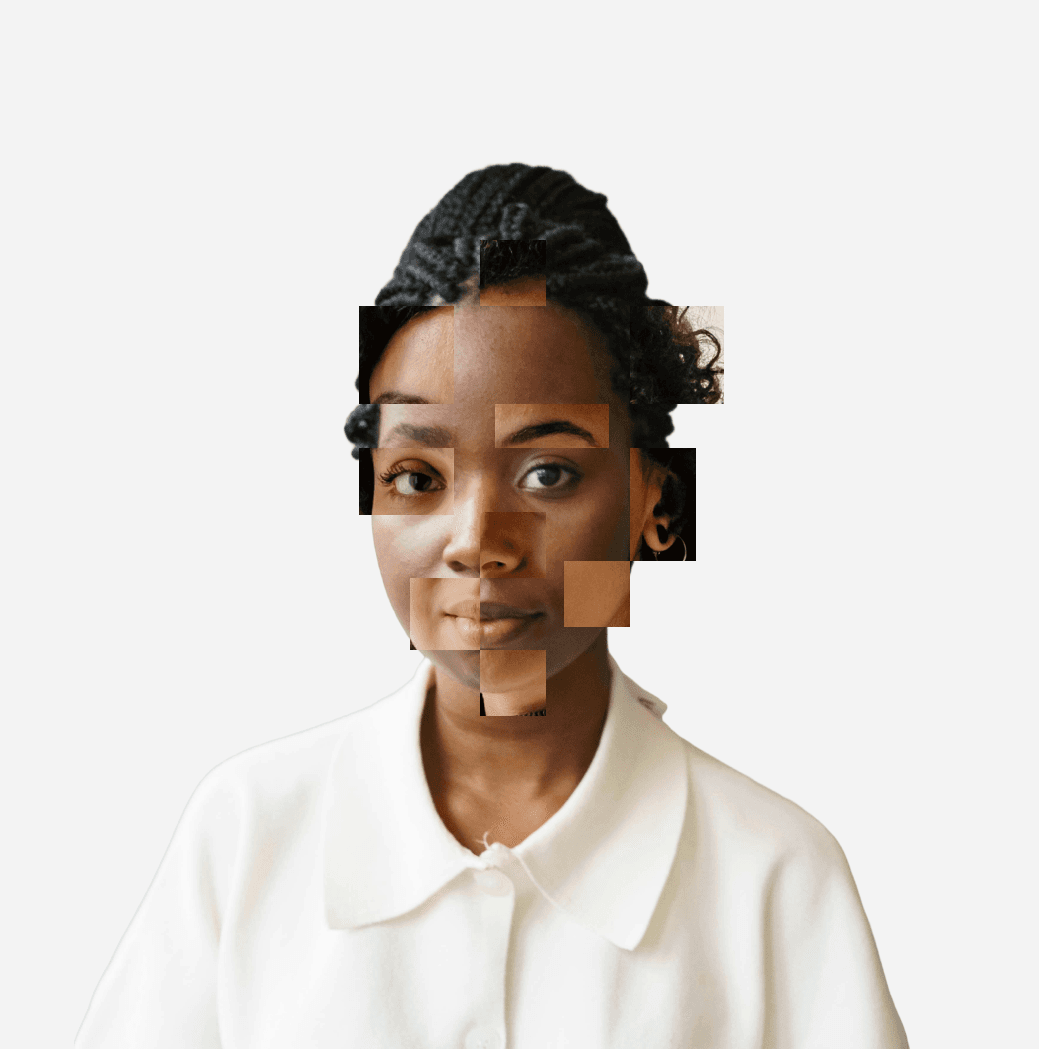
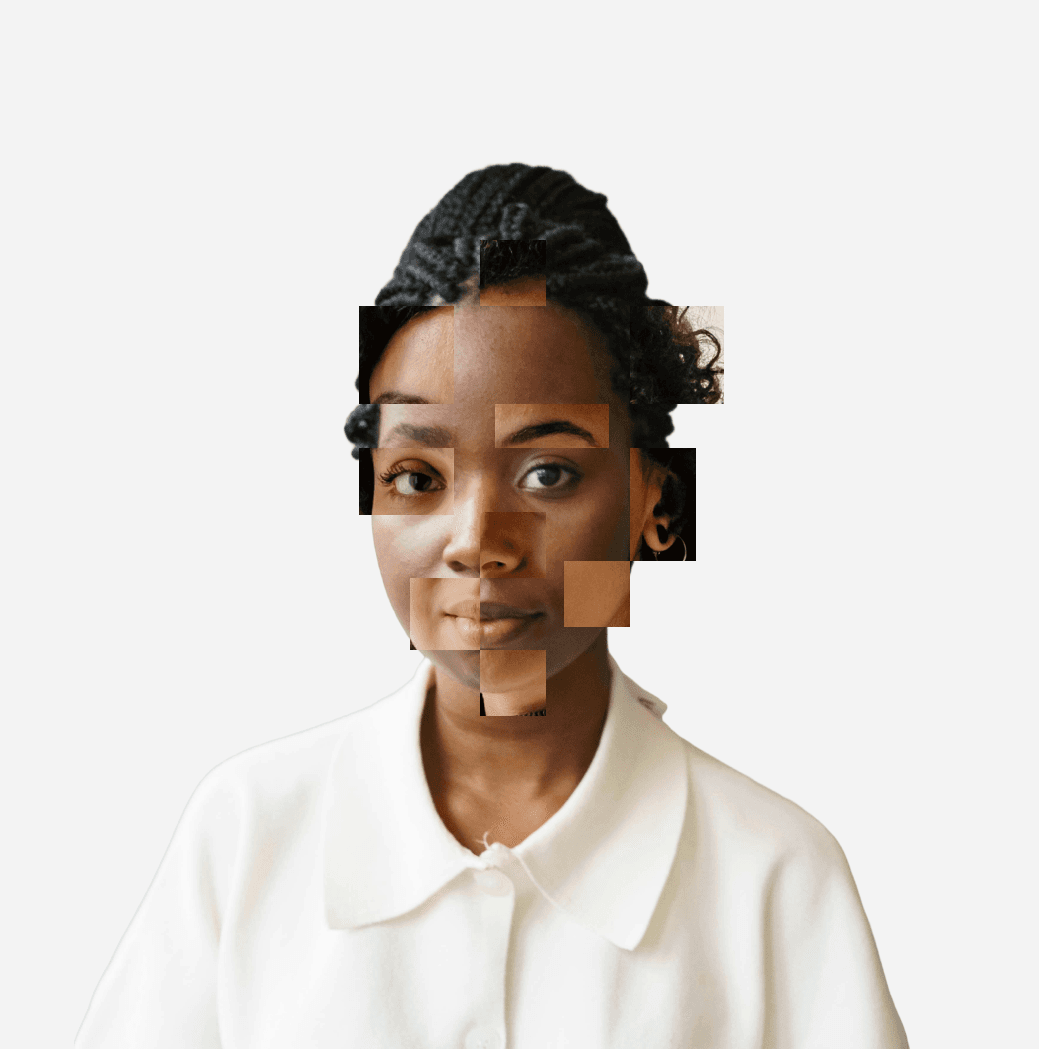
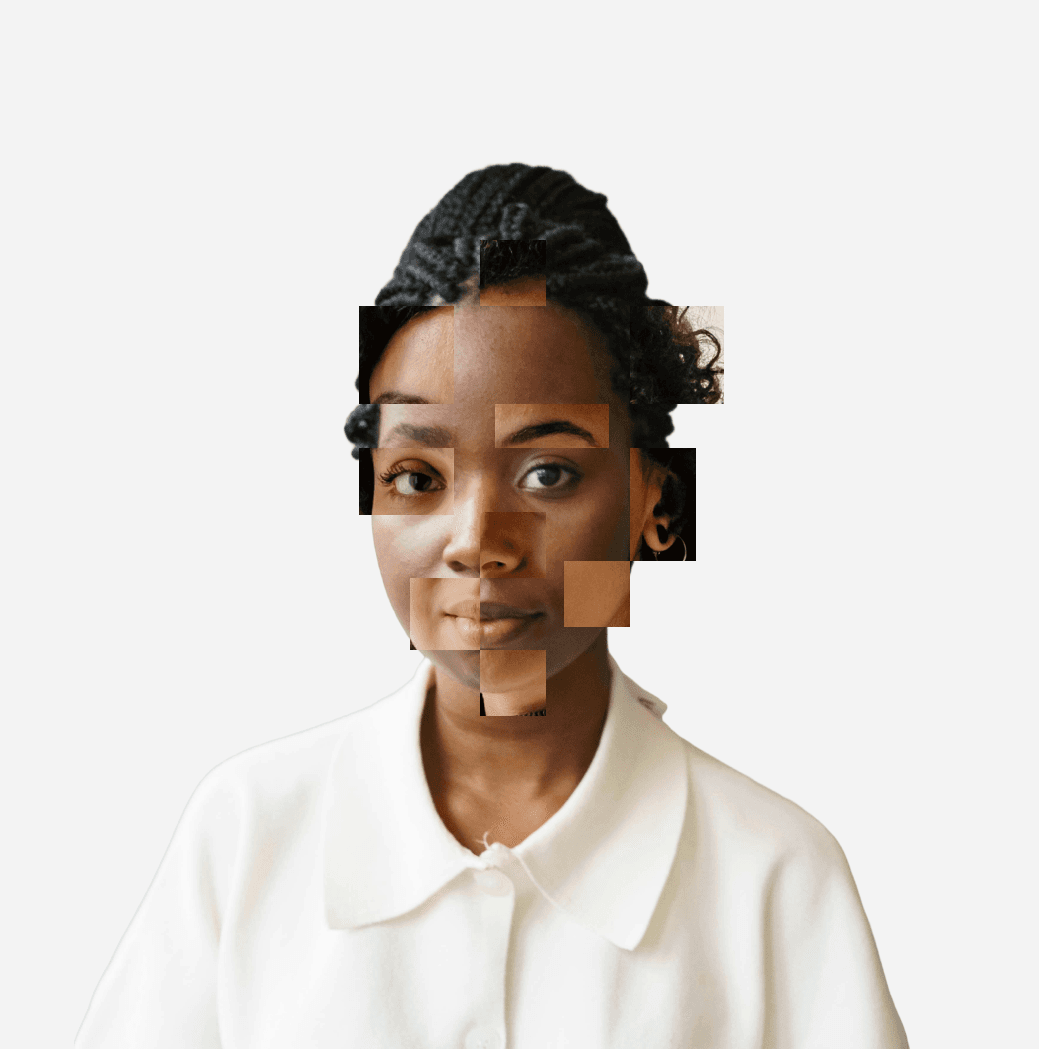
Liveness Detection
Mitigation against deepfakes and static photos (model details in the Technical Matrix)
Data Sovereignty
AES-256 encryption at rest and TLS in transit with zero-knowledge architecture.

Hard-Coded Recipient Integrity



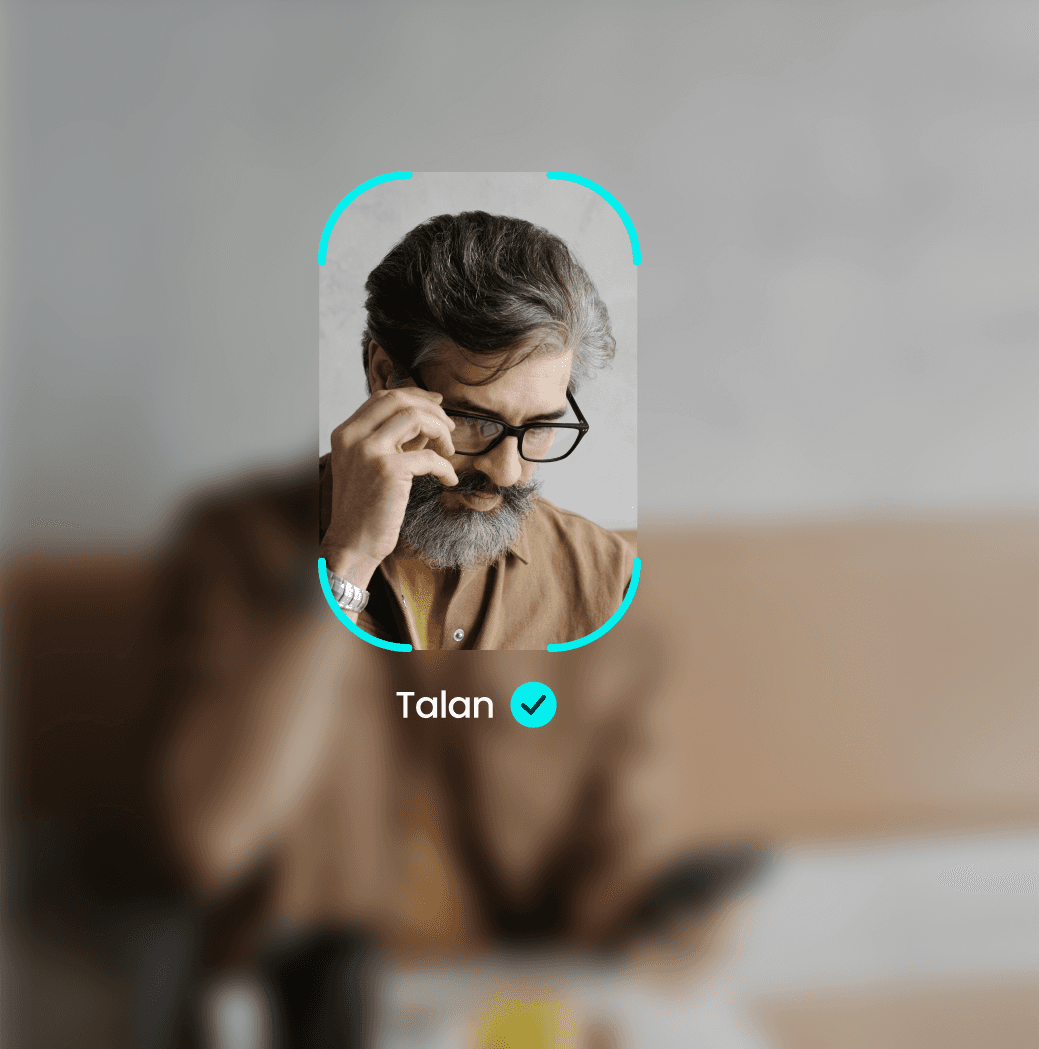
Evidence of Sight
Biometric confirmation that the intended eyes, and only those eyes, are on the screen.
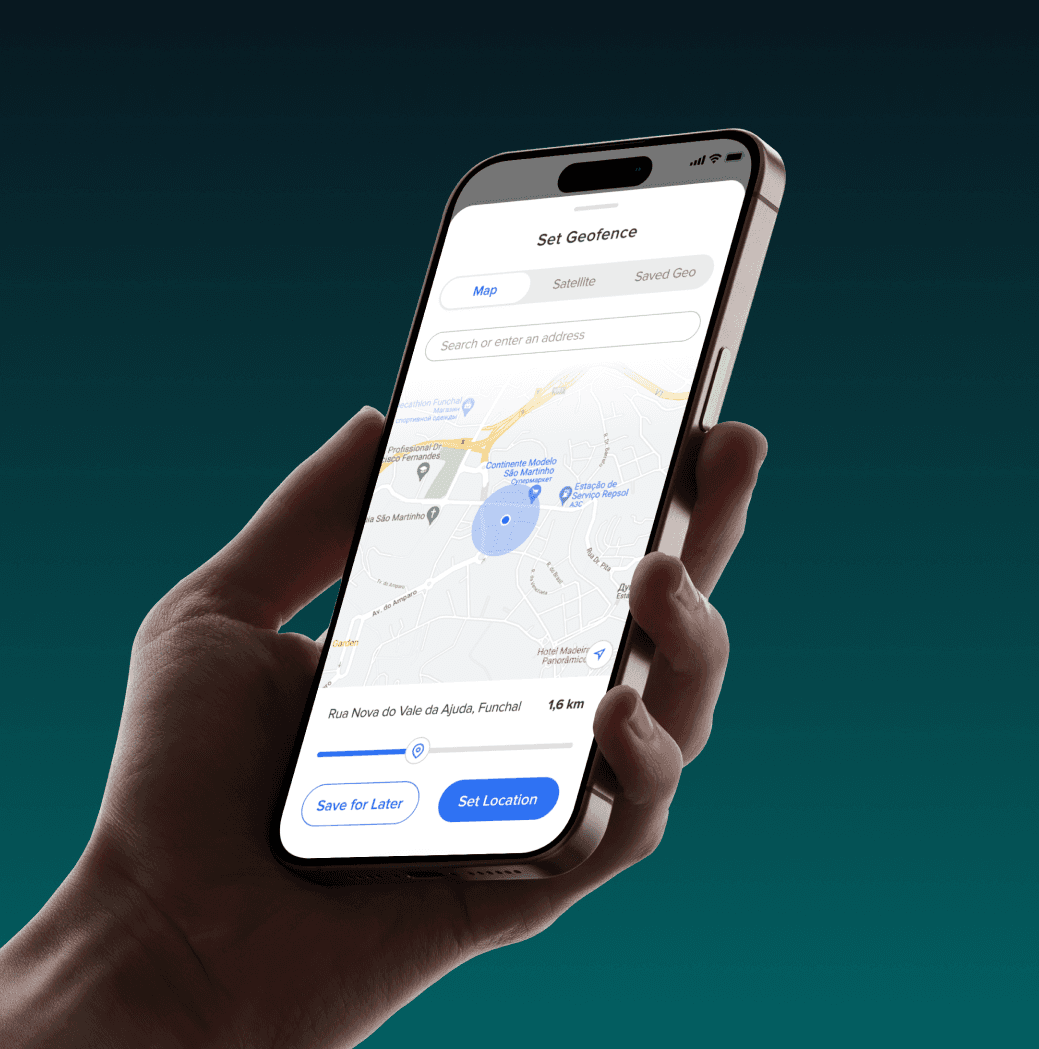
Hardware-Locked Geofencing
Precise, GPS-locked access boundaries ensuring sensitive data stays within authorised zones.
Liveness Detection
Mitigation against deepfakes and static photos (model details in the Technical Matrix)
Data Sovereignty
AES-256 encryption at rest and TLS in transit with zero-knowledge architecture.

Hard-Coded Recipient Integrity



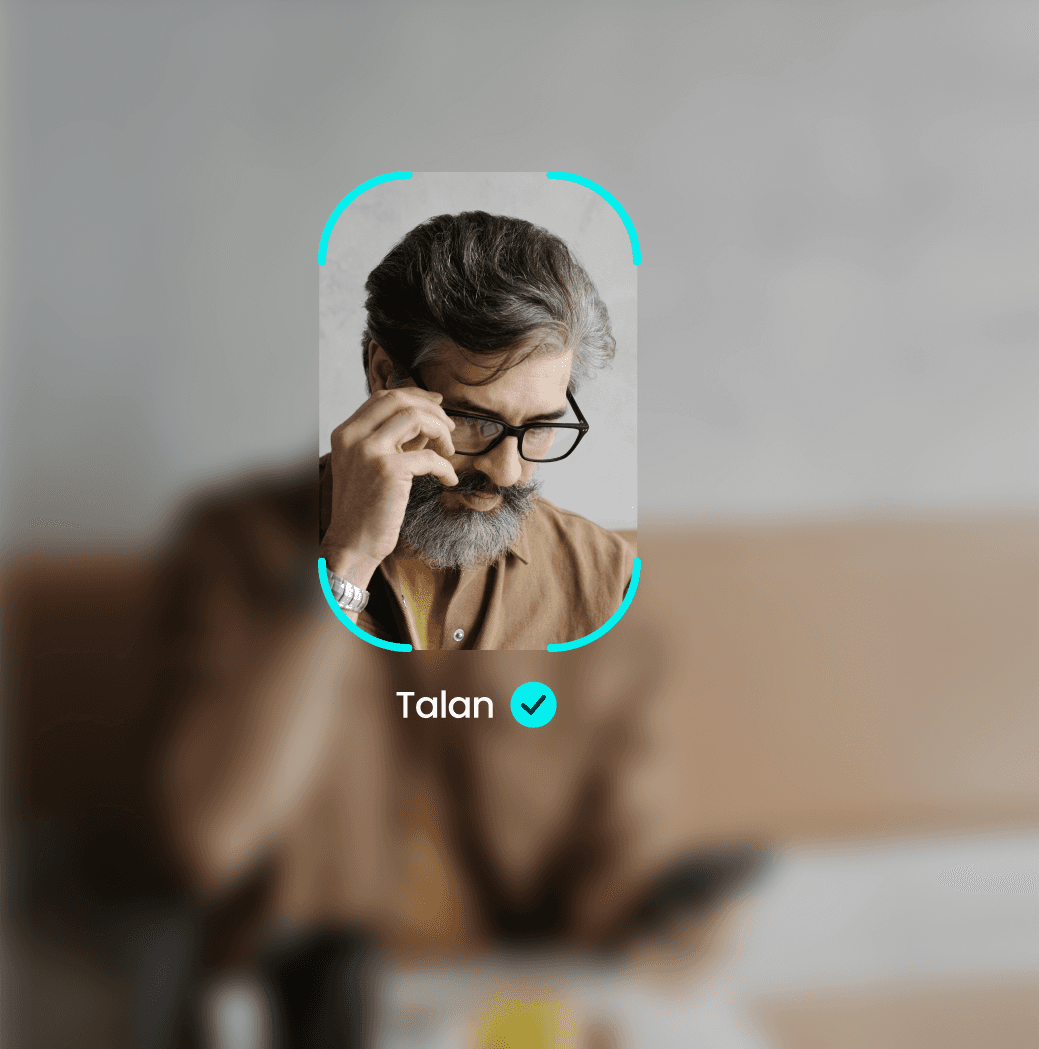
Evidence of Sight
Biometric confirmation that the intended eyes, and only those eyes, are on the screen.
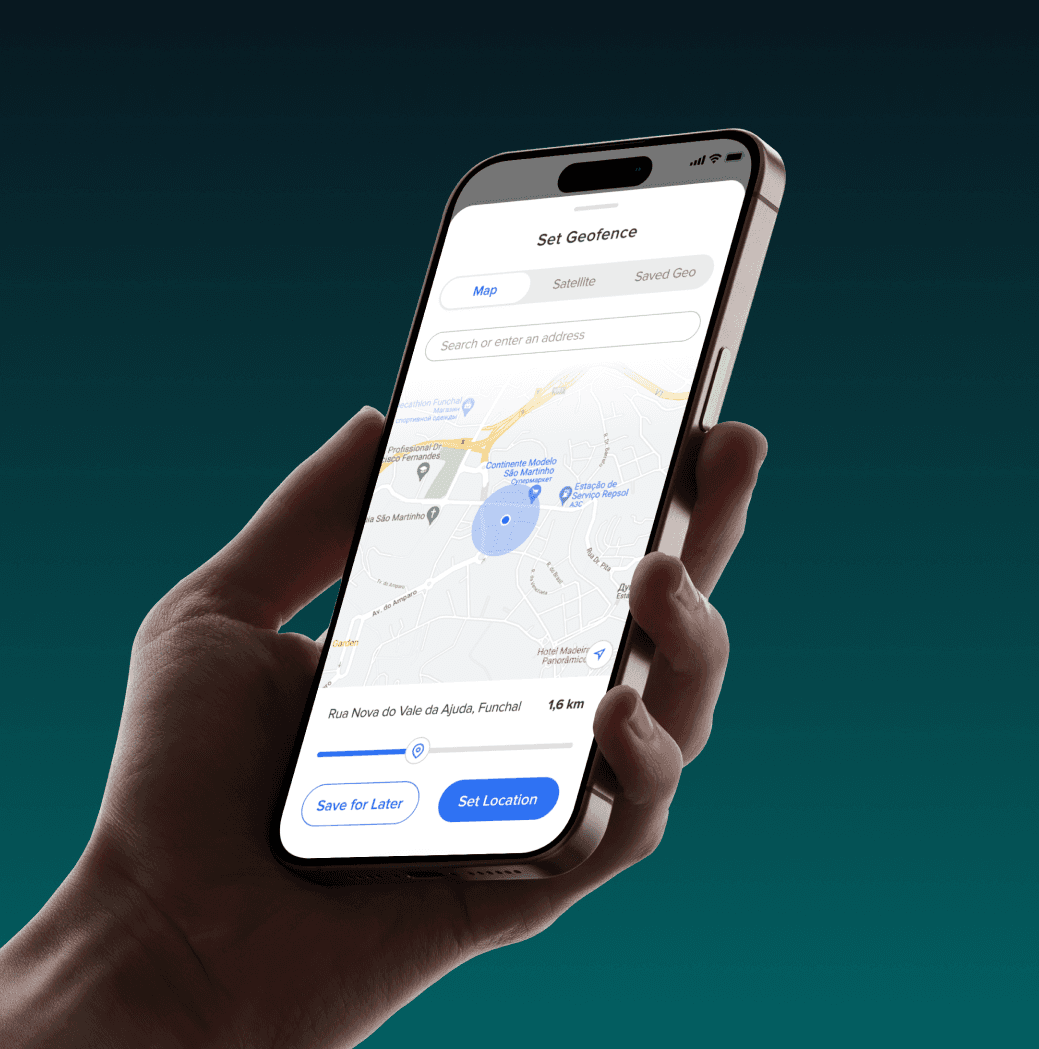
Hardware-Locked Geofencing
Precise, GPS-locked access boundaries ensuring sensitive data stays within authorised zones.
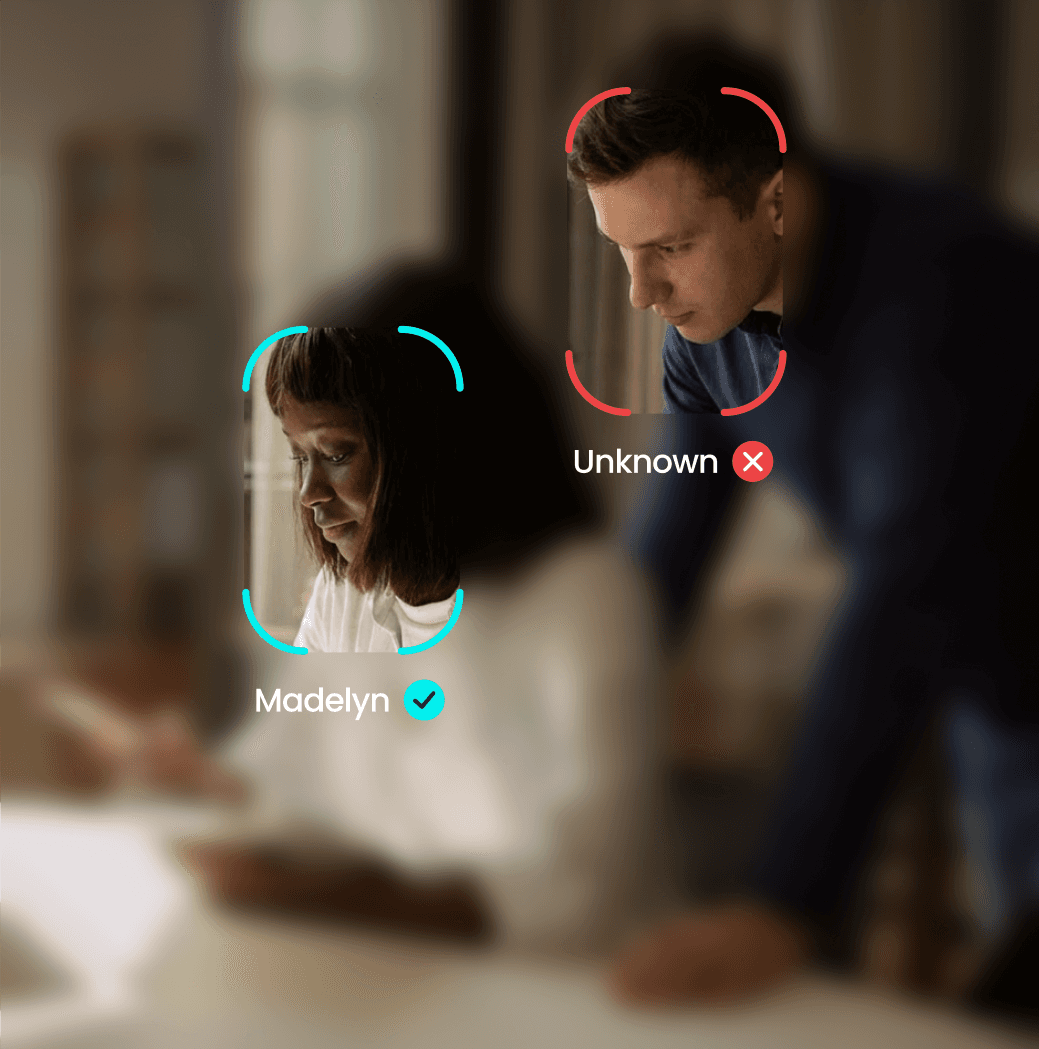
Liveness Detection
Mitigation against deepfakes and static photos (model details in the Technical Matrix)
Data Sovereignty
AES-256 encryption at rest and TLS in transit with zero-knowledge architecture.
COMPLIANCE
Engineered for Regulatory Rigour
Every confidential file sent without human verification increases exposure under CRB 24-hour disclosure rules.

CRB Compliance Ready

NIS2 & DORA Alignment

Liability Mitigation
COMPLIANCE
Engineered for Regulatory Rigour
Every confidential file sent without human verification increases exposure under CRB 24-hour disclosure rules.

CRB Compliance Ready

NIS2 & DORA Alignment

Liability Mitigation
COMPLIANCE
Engineered for Regulatory Rigour
Every confidential file sent without human verification increases exposure under CRB 24-hour disclosure rules.

CRB Compliance Ready

NIS2 & DORA Alignment

Liability Mitigation

Frequently Asked Questions
Does YEO store biometric data?
What happens if liveness/face-lock fails?
Does this work on unmanaged or BYOD devices?
What does the Evidence of Sight log contain?
How does it integrate with SIEM workflows?


Build a More Resilient Identity Architecture.
Own the Evidence of Sight. Download the Technical Matrix to see how YEO eliminates single points of failure.


Build a More Resilient Identity Architecture.
Own the Evidence of Sight. Download the Technical Matrix to see how YEO eliminates single points of failure.


Build a More Resilient Identity Architecture.
Own the Evidence of Sight. Download the Technical Matrix to see how YEO eliminates single points of failure.